ARCrypt Ransomware Adapts TOR Communication Channels to Avoid Detection

A newly developed Linux variant of AR crypt malware developed with GO language started concentrating on worldwide.
The emergence of AR Crypt malware used to be considered within the year of Aug 2022, able to heart of attention on both Linux and Windows machines.
Based totally on Cyble Study, the recent variant as a lot as this level its ways and techniques to work alongside with victims to evade detections.
Prognosis of Contemporary Variant
Unlike the dilapidated variant, the recent variant communicates with victims by replicate sites, and risk actors originate uncommon chat sites for every sufferer.
Also, it instructs victims to originate a client profile on the TOX messaging page for verbal exchange and affords a wonderful buy if the ransom used to be paid in Monero.
Since the assault vector of the ransomware is unknown, once executed the payload the ransomware copies to the %TEMP% directory and assigns a random six-digit higher alphanumeric payment.
Later, it deletes the actual ransomware binary utilizing the expose “cmd /c DEL “%SAMPLEPATH%” &EXIT,” where A batch script used to be primitive to get rid of the preliminary executable file in dilapidated versions
To boot to that, it terminates processes connected to anti-malware, backup, and recovery to bound encryption to evade detection from EDR.
Lastly, this ransomware delivers a ransom existing sooner than encrypting the recordsdata; it encrypts the recordsdata with the extension “.crYpt”, whereas the older variant makes use of the “.crypt” extension.
The binaries within the ransom existing verbalize the victims to reasonably a pair of Tor sites for verbal exchange, which portion the same client interface however grasp reasonably a pair of URLs.
In overall, ransomware TAs encompass all the replicate sites within the ransom existing to make optimistic accessibility for victims. This draw enables victims to safe true of entry to an various location if one becomes inaccessible.
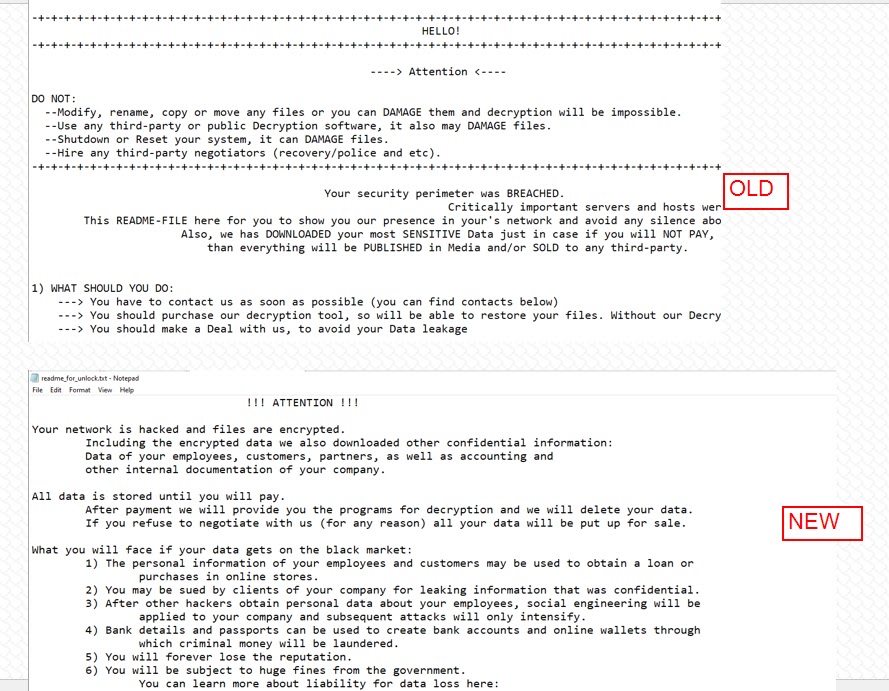
This ARCrypt ransomware rigidity introduces a particular ransom existing that most attention-grabbing vaguely resembles the sooner ransom existing.
An as a lot as this level model of the ARCrypt ransomware has emerged with distinct adjustments. Researchers imagine the TA who created the ARCrypt malware is attempting to quit out of the public assume.
Indicators of Compromise
| Indicators |
| 9b80a70be01700866a667085aad93b5a0408d6208440ef3caf7078361897f47c911de543a933ebeb8bec26881b2d191f5034b7d6cacbb8d2cc06eeb7327f752fd0fab24d |
| 7df9c7e23c2a1f8d3d87cd2460bb275cb589fccc88bd05df102b7584c356fce21be1de5894e227ad918034ae9b569a380a5e6c8928428862236395e3357a085b03f25fef |
| 90aeedae5648c65ca3c3fb2ac038033744069c654987abb00ce9068dd856bd2065a20aa9e56eba93a0f3fab5e26c992a18cb6754c4b1a688e26a73c424d272babeab503c |
| a84957660902eb17fd021f3d187fb787cb3700cb561a449e6ff88978fb4ce1495982fe95b38807e5d6c4c4ae6811058fd868256abd6ed95f440e7f27ea81408bb9ee27fb |
| a0aad92f585dfc6ac762b5fc829e6fba9ad2ae2c7fda526131ad6d535b21fe55d027d3aa4f2e40e6353a2430a80824d113268b5cdb28a0ddb079418be05ba79dea608410 |
Source credit : cybersecuritynews.com

