Beware of Fake Trading Apps on Google Play & App Store that Steal Your Money
.webp)
A recent investigation unveiled a trend of fraudulent procuring and selling apps on Google Play and the App Store designed to trick unsuspecting users out of their arduous-earned money.
This text delves into the mechanics of these scams, highlighting the urgent need for vigilance among digital finance users.

Surge in Pig-Butchering Rip-off
The timeframe “pig-butchering scam” could perchance perchance sound weird and wonderful, however its implications are removed from benign.
Are you from SOC and DFIR teams? – Join With 400,000 self ample Researchers
Malware analysis can even be immediate and straightforward. Honest accurate let us tag you easy easy methods to:
- Work along with malware safely
- Space up digital machine in Linux and all Home windows OS variations
- Work in a team
- Obtain detailed reports with maximum data
Will salvage to you like to deserve to check all these ingredients now with for free entry to the sandbox:
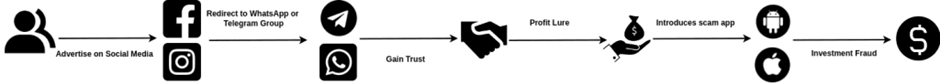
Originating in Southeast Asia, this scam entails fattening the pig (the victim) by constructing a relationship and belief over time, handiest to slaughter it financially within the end.
India has witnessed a valuable surge in such scams, with cybercriminals deploying sophisticated social engineering ways to trap victims into their traps.
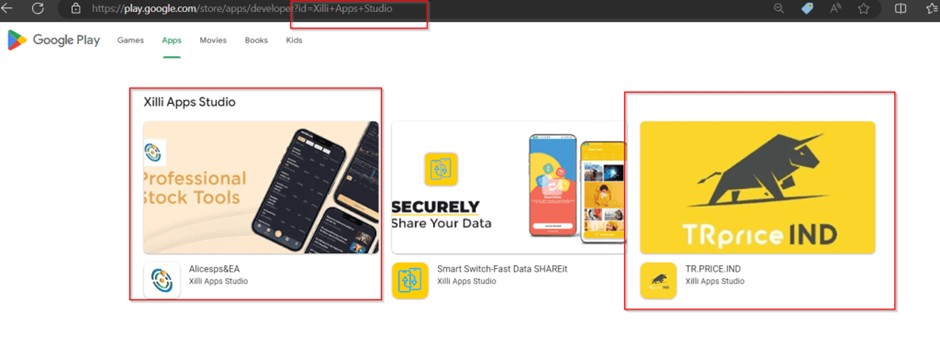
A startling revelation within the investigation is the compromise of legit developer accounts on standard app stores.
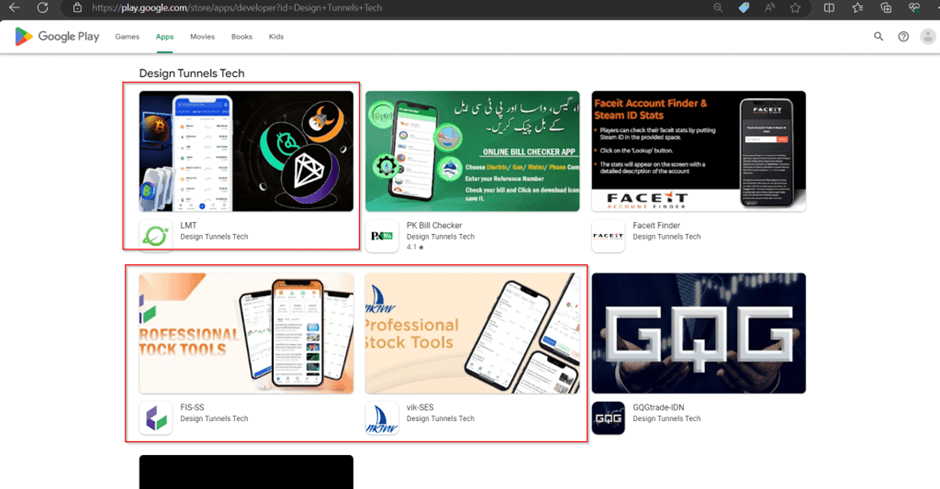
Cybercriminals salvage infiltrated these accounts, the utilization of them as a launchpad to submit malicious procuring and selling apps.
This breach undermines the protection protocols of predominant app stores and locations limitless users susceptible to economic theft.
Fake Trading Applications
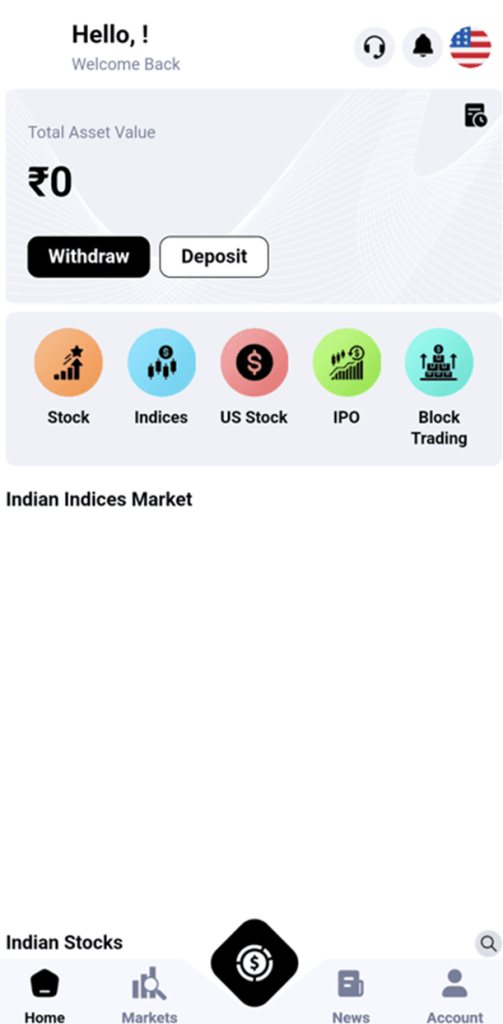
The core of this scam lies in groundless procuring and selling capabilities meticulously designed to imitate legit ones.
These apps provide animated ingredients and promises of high returns, drawing users into a web based of deceit.
Once set in, they serve as conduits for monetary and deepest data theft, ensuing in mammoth monetary losses for the victims.
Cyble Be taught and Intelligence Labs (CRIL) has seen a mighty surge in pig-butchering scams focusing on Indian traders who deserve to make the quite loads of the stock market.
Adding a layer of authenticity to their plot, scammers salvage resorted to increasing fabricated articles and news reviews.
These pieces fundamentally feature fraudulent endorsements from celebrities or reputed monetary consultants, extra deceptive doable victims.
The sophistication of these articles makes it extra and extra complicated for users to distinguish between legit and fraudulent sources.
The digital finance panorama is fraught with dangers, underscored by the alarming upward push in fraudulent procuring and selling apps and pig-butchering scams.
Users ought to exercise utmost caution, verifying the legitimacy of any app sooner than downloading and refraining from sharing deepest or monetary data online.
It’s imperative for app stores to toughen their security features and for authorities to take decisive motion in opposition to these cybercriminals.
In the intervening time, awareness and vigilance are the correct defenses in opposition to these digital predators.
IOCs
| Indicators | Indicator Form |
| faf7a001250ef1dbd2d6eaf8eabbd8d589c0960e871325808a7a1a76619c4b4f 87196e5cda572d63c43d52df200e823a9811e33a ecce84056298bc3bcc8c17d6ed12a29b |
SHA256 SHA1 MD5 |
| app[.]panth-ss[.]vip | Domain |
| 0a2fffb84d58dbf3cb2a50fd15d3cda9b3998c85c0424e29bf0964cc6bbda920 2288add2292e026cb32933943d2c9f105e57ed8d a522af373e24042e4b1995a186cfed6a |
SHA256 SHA1 MD5 |
| app[.]yongljt[.]com | Domain |
| 52c36d2e1c5df64b96e017625fdd2d1c07e2a0b741c155735d09c068b23d54ad 53c40428b48050ecd851f58b020629f58b6bd18f e1b935f23c49ac0b1176c3b650e5bc12 |
SHA256 SHA1 MD5 |
| hxxps://www[.]inueyd[.]com/?v=3 | Domain |
| Giottusmh[.]com giottusmk[.]com |
Domain |
| 34.131.1[.]213 | IP |
That you simply would possibly perchance perchance perchance also block malware, along with Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware safety. All are extremely corrupt, can wreak havoc, and injury your community.
Stay unsleeping to this level on Cybersecurity news, Whitepapers, and Infographics. Put together us on LinkedIn & Twitter.
Source credit : cybersecuritynews.com


