BingBang – A New Bing Vulnerability that Can be Exploited Without Executing a code

Azure Filled with life Itemizing (AAD) has a new attack vector that affected Microsoft’s Bing.com, based on Wiz Overview. A frequent AAD misconfiguration is the attack vector, making misconfigured apps at risk of intrusion.
Microsoft’s AAD, a cloud-based identification and internet entry to administration (IAM) service, is the frequent authentication methodology for Azure App Providers and products and Azure Capabilities purposes.
“The researchers found several Microsoft purposes at risk of this attack, considered one of which become a Affirm material Management Plan (CMS) that powers Bing.com,” says Wiz researchers.
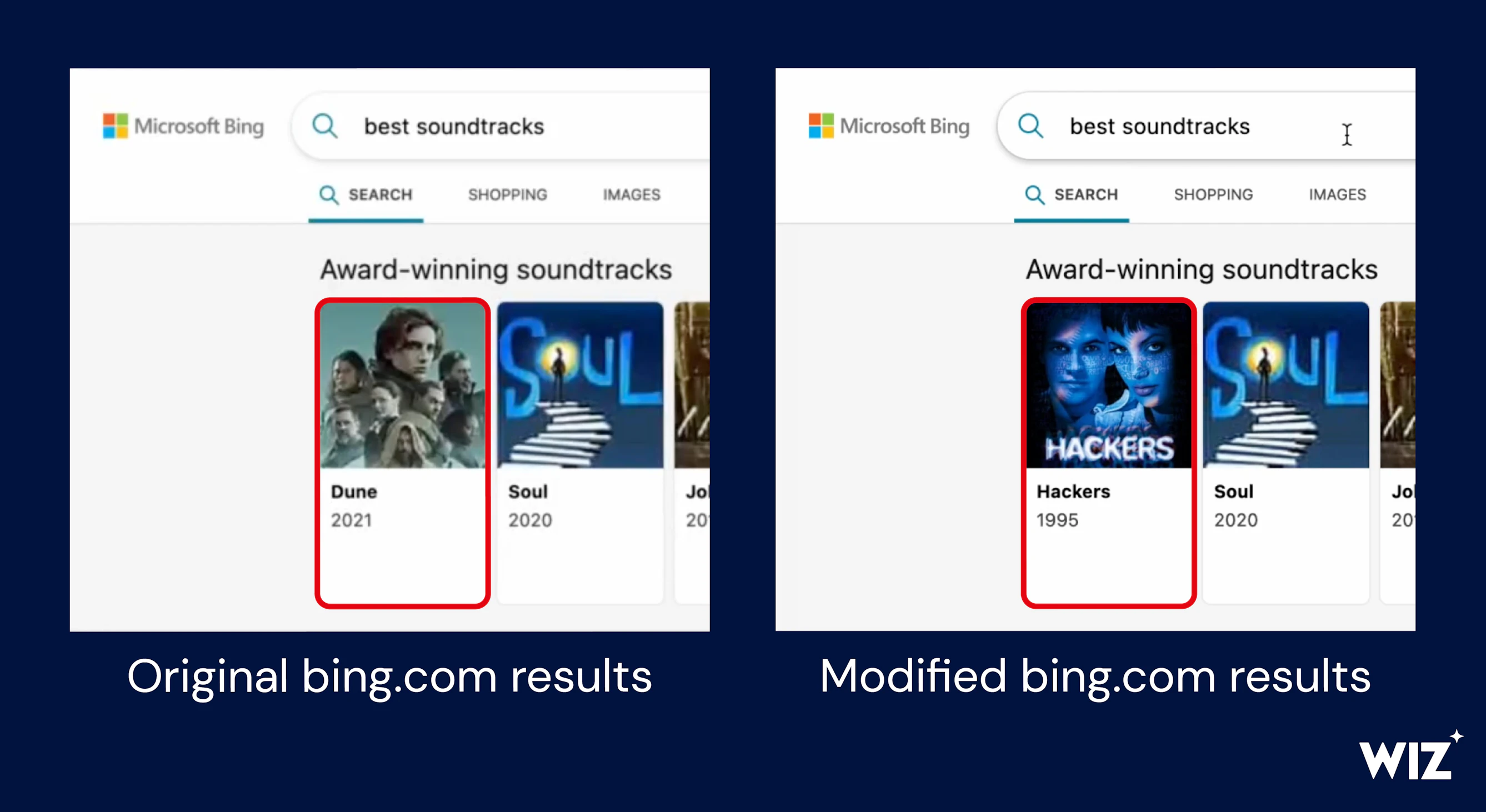
“This allowed them to snatch over Bing.com functionality, modify search results, and doubtlessly allow the Place of work 365 credential theft of hundreds of thousands of Bing customers. These credentials in turn granted internet entry to to customers’ non-public emails and documents”.
Unsafe Configuration Chanced on in AAD
On the total, single-tenant, multi-tenant, non-public accounts, or a mixture of the closing two are the many account internet entry to alternatives AAD offers.
Any particular person from any Azure tenant may perhaps well well also log in to a multi-tenant app. The developer need to take a look at the actual person’s usual tenant in a multi-tenant app and affords internet entry to properly. Any person with an Azure account from anyplace worldwide may perhaps well well also internet entry to the app if they fail to validate this files well.
Researchers shriek builders may perhaps well well also no longer constantly perceive this Shared Accountability structure, so setup and validation errors are progressively made.
Practically 25% of the multi-tenant apps researchers analyzed at some point soon of the investigation had been glaring weaknesses.”Bing Minutiae,” a Microsoft-produced app, become on the checklist.
The researchers may perhaps well well also internet entry to this app with their Azure particular person due to the it become misconfigured. They then found a Affirm material Management Plan (CMS) linked to Bing.com.
“A malicious actor touchdown on the Bing Minutiae app online page may perhaps well well also therefore receive tampered with any search term and launched misinformation campaigns, besides to phished and impersonated diversified internet sites,” Wiz researchers point out.
The researchers learned that Bing and Place of work 365 had been linked and ought in an effort to add infamous-place scripting (XSS) payload into Bing.com, allowing them to compromise any particular person’s Place of work 365 token.
“With a stolen token, a doubtless attacker may perhaps well well also internet entry to Bing customers’ Place of work 365 files, along with Outlook emails, calendars, Groups messages, SharePoint documents, and OneDrive files”, researchers.
So, a tainted actor with the identical internet entry to may perhaps well well receive feeble primarily the most celebrated search results to hijack them with the identical payload and leak hundreds of thousands of customers’ sensitive files.
Suggestion
Mag Data, Centralized Notification Provider (CNS) API, Contact Heart, PoliCheck, Vitality Automate Weblog, and the file administration machine COSMOS had been also amongst the within Microsoft purposes harmed by the misconfiguration.
Directors are encouraged to double-take a look at their purposes’ configurations to be definite that that multi-tenant internet entry to is determined up wisely or to swap to single-tenant authentication if multi-tenancy is pointless.
It’s also educated to leaf by logs for the previous job for inclined purposes (AAD logs, nonetheless, are insufficient for that).
Microsoft mercurial patched its inclined apps and modified the functioning of several AAD aspects to minimize buyer publicity. Whiz reported the initial Bing malicious program on January 31, and Microsoft rectified it that day. The tech huge awarded a malicious program bounty of $40,000.
Linked Read:
- EmojiDeploy Vulnerability in Azure Let Attackers Accomplish Faraway Code
- Microsoft Azure Providers and products Vulnerability Let Attackers Blueprint Unauthorized Procure admission to
- Azure Provider Fabric Explorer Flaw Let Attacker Blueprint Administrator Privileges
- Cloud-Essentially based fully Cryptocurrency Miners Abuse GitHub Actions & Azure to Mine Cryptocurrency
- Azure Database for PostgreSQL Let Attacker to Bypass Authentication and Blueprint Procure admission to
Source credit : cybersecuritynews.com


