Hackers Allegedly Leaked CrowdStrike’s Threat Actor Database
Hackers Allegedly Leaked CrowdStrikeâs Threat Actor Database
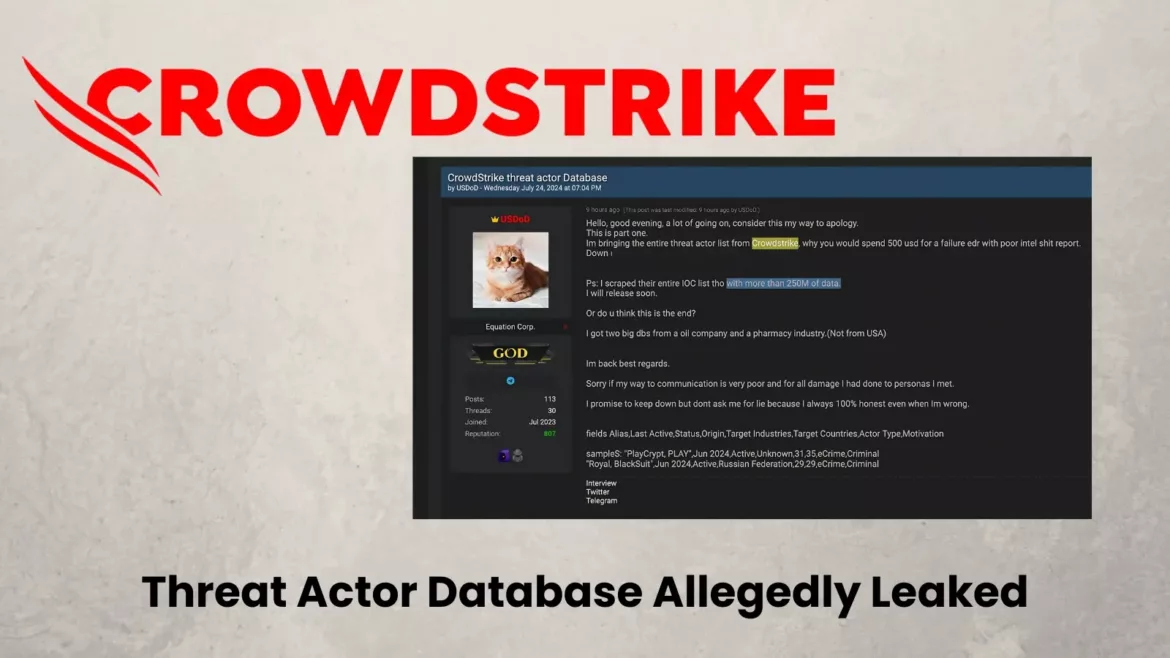
A hacktivist entity known as USDoD has claimed to contain leaked CrowdStrike’s “whole threat actor list” and alleged possession of the company’s “whole IOC [indicators of compromise] list”, which contains over 250 million records aspects.
On July 24, 2024, the USDoD community announced on the English-language cybercrime dialogue board records leak forums that they had obtained and leaked CrowdStrike’s whole threat actor database.
The community supplied a hyperlink to earn the alleged list and shared sample records fields to substantiate their claims.
The leaked records reportedly entails:
- Adversary aliases
- Adversary self-discipline
- The final involving dates for every adversary
- Put/Country of Adversary Foundation
- Sequence of focused industries and worldwide locations
- Actor sort and motivation

The sample records contained “LastActive” dates as much as June 2024, whereas the Falcon portal’s final involving dates for some actors lengthen to July 2024, suggesting the aptitude timeframe of the records acquisition.
Cyber Press researchers acknowledged that they were able to contain a look at a few of the documents leaked

.webp)
USDoD has a historical previous of exaggerating claims, seemingly to augment its recognition within hacktivist and eCrime communities. For event, they previously claimed to contain conducted a hack-and-leak operation concentrated on a talented networking platform, which become once later refuted by industry sources as mere internet scraping.
Since no longer decrease than 2020, USDoD has engaged in both hacktivism and financially motivated breaches, essentially the utilization of social engineering ways. Nowadays, they’ve focused on excessive-profile focused intrusion campaigns and contain sought to magnify their activities into administering eCrime forums.
USDoD moreover claimed to personal “two plentiful dbs from an oil company and a pharmacy industry (no longer from USA)”. On the opposite hand, the connection between these claims and the alleged CrowdStrike records acquisition stays unclear.
The capacity leak of CrowdStrike’s threat actor database could well perhaps vastly impact cybersecurity measures.
- Compromise of ongoing investigations
- Publicity of tracking concepts for malicious actors
- Doable advantage for cybercriminals in evading detection
The story unfolds following the CrowdStrike update, which causes the Home windows machine to ride the Blue Veil of Loss of life (BSOD) error.
CrowdStrike’s Response
CrowdStrike, a main cybersecurity company known for its threat intelligence and incident response providers, has replied. The corporate acknowledged, “The threat intel records well-known in this whisper is supplied to tens of hundreds of purchasers, partners, and prospects â and hundreds and hundreds of customers. Adversaries exploit recent events for consideration and attain. We dwell committed to sharing records with the community.”
Whereas USDoD has been focused on legitimate breaches, its credibility in this teach case is questionable. Their historical previous of exaggeration, the inconsistencies within the leaked records, and CrowdStrike’s response all forged doubt on the authenticity and severity of the claimed leak.
Source credit : cybersecuritynews.com