D-Link NAS Command Injection Flaw : 92,000 Devices Affected
.webp)
A original recount injection vulnerability and a backdoor story had been narrate in D-Link Community Linked Storage gadgets, which impacts D-Link NAS gadgets, along side DNS-340L, DNS-320L, DNS-327L, and DNS-325, amongst others.
This exists in the nas_sharing.cgi file of these gadgets and the recount injection vulnerability (CVE-2024-3273) exists in the system parameter.

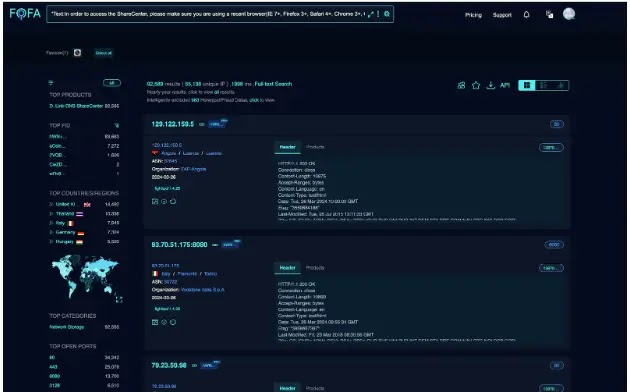
As a matter of reality, these vulnerabilities enjoy an tag on extra than 92,000 D-Link NAS gadgets that are exposed over the web.
However, patches for these vulnerabilities had been printed by D-Link and users are impressed to patch them as rapidly as doable.
Vulnerability Facts
In keeping with the reports shared, if these vulnerabilities are subjected to exploitation, it could presumably allow a threat actor to assemble an arbitrary recount execution on the affected system and accumulate earn entry to to nonetheless data.
AI-Powered Protection for Enterprise E-mail Safety
Trustifi’s Superior threat protection prevents the widest spectrum of sophisticated assaults earlier than they attain a client’s mailbox. Strive Trustifi Free Threat Scan with Subtle AI-Powered E-mail Protection .
Additionally, a threat actor can also potentially assemble a system configuration alteration or denial of service by specifying a recount during the recount parameter.
The nas_sharing.cgi is a CGI (General Gateway Interface) script that has a hardcoded story that would possibly maybe well presumably be feeble as a backdoor through username and password publicity.
The exploitation within reason easy as the parameter anticipate entails a username (client=messagebus) and an empty password (passwd=). This would possibly maybe well present unauthorized earn entry to for threat actors with none appropriate kind authentication.
Additional, recount injection would possibly maybe well merely additionally be finished during the Arrangement parameter, which carries a base64-encoded price that, when encoded, becomes a recount.
Exploitation
A threat actor can craft a malicious HTTP anticipate concentrated on the /cgi-bin/nas_sharing to make essentially the most of this vulnerability.cgi endpoint.
The ensuing response of this HTTP anticipate includes the decoded system parameter price despatched in the anticipate.

Affected Products
- DNS-320L Version 1.11, Version 1.03.0904.2013, Version 1.01.0702.2013
- DNS-325 Version 1.01
- DNS-327L Version 1.09, Version 1.00.0409.2013
- DNS-340L Version 1.08
Customers of these merchandise are suggested to upgrade to the most recent variations in show to live the exploitation of these vulnerabilities by threat actors.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide
Source credit : cybersecuritynews.com


