LockBit Ransomware is Back From the Dead : Is Your SOC/DFIR Team Prepared?
LockBit Ransomware is Support From the Ineffective : Is Your SOC/DFIR Body of workers Ready?
Law enforcement disrupted LockBit ransomware operations in February, seizing infrastructure and their net place of dwelling.
Regretfully, the victory looks to had been transient. The crowd’s leading members weren’t detained, and Operation Cronos’s defeat used to be simplest transient for the explanation that neighborhood bounced again in a matter of days.
A surge in LockBit relate days after the takedown indicated renewed attacks whereas the team utilized up in the past encryption instruments and directed victims to contemporary servers.
Researchers from ANY.RUN seen by the Interactive Malware Sandbox Application that the incident mirrors previous events in which dismantled ransomware groups re-emerged with improved instruments. REvil emerged quickly after GandCrab’s takedown, likely utilizing the latter’s offer code.
About LockBit
LockBit is a cybercriminal organization offering ransomware and developed persistent likelihood (APT) capabilities. Their ransomware encrypts victim methods, essentially targeting Residence windows, and may maybe perchance additionally additionally hit Linux and MacOS.
Working as a Ransomware-as-a-Provider (RaaS), LockBit developers promote their instruments and infrastructure to affiliates, who then commence the attacks, which permits them to live nameless whereas benefiting from a broader range of attackers.
The neighborhood has claimed responsibility for a huge alternative of excessive-profile incidents, extorting over $120 million from victims.
Incorporate ANY.RUN into your company for speedy and straightforward malware evaluation
Are you from SOC, Threat Compare, or DFIR departments? If so, you will want the choice to be part of an on-line community of 400,000 honest security researchers:
- Real-time Detection
- Interactive Malware Evaluation
- Easy to Study by Contemporary Safety Body of workers members
- Procure detailed reports with most recordsdata
- Build Up Virtual Machine in Linux & all Residence windows OS Variations
- Work alongside with Malware Safely
Procure a personalised demo of ANY.RUN for your security team:
It highlights the significance of utilizing transient disruptions to gaze seized infrastructure and prepare for doable evolutions of the likelihood.
Support from Ineffective
Per ANY.RUN gaze that used to be shared with Cyber Safety Records accepted a duration of inaction followed by a spike, as LockBit detections in our sandbox reached 0 after which began to develop, starting just a few days after the takedown.
The LockBit ransomware gang has resumed its attacks. Now, theyâre utilizing up in the past encryptors and ransom notes that consequence in contemporary servers.
Per the ANY.RUN Sandbox Evaluation, In want to rebranding, the LockBit gang promised to come again with enhanced infrastructure and up in the past safety features to discontinue law enforcement from reaccessing their descriptors.
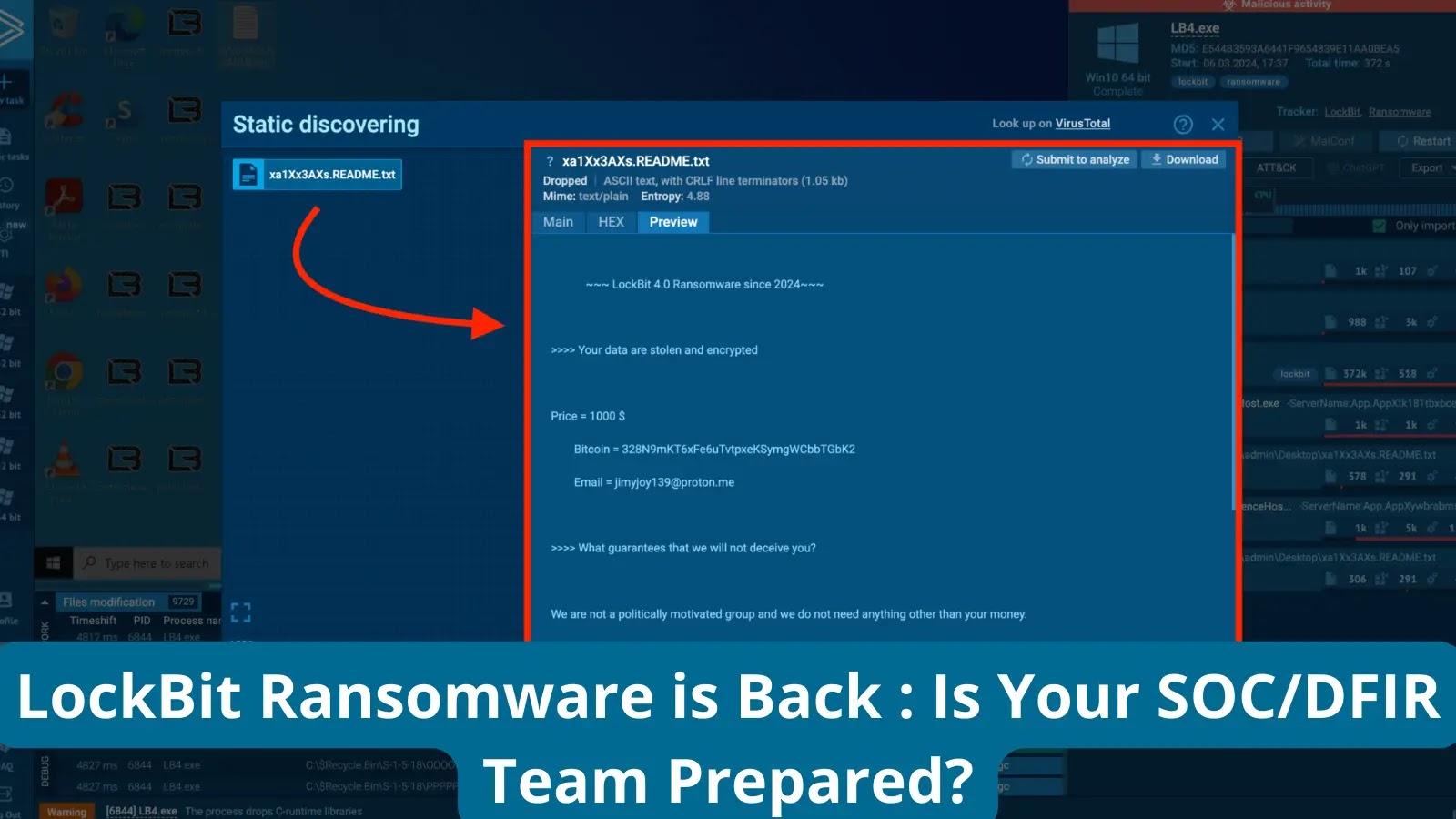
Inspecting LockBit in ANY.RUN
A prevalent strain, LockBit ransomware, is actively being developed. No matter a most modern takedown by law enforcement, its creators have a tendency to change the code to evade detection. Organizations ought to composed be involving, because the LockBit infection remains a basic likelihood.
Learning LockBit’s attack patterns (TTPs) and Indicators of Compromise (IOCs) is an valuable for Safety Knowledge and Event Management (SIEM) and Threat Intelligence Platform (TIP) methods to identify and isolate intrusions sooner than file encryption occurs.
The most contemporary variant, LockBit 4.0, displays adjustments: it now now not modifies the desktop wallpaper, and the decryption course of is tremendously slower. Also, now not like its predecessor, version 4.0 would now not self-delete after encryption.

LockBit ransomware, which is acknowledged for targeting Residence windows essentially but can have the choice to compromising Linux and MacOS methods, has re-emerged with up in the past instruments and infrastructure after a most modern takedown.
This notorious ransomware neighborhood is accountable for extorting over $120 million from 2,000 victims, and knowing LockBit’s attack patterns, tactics, programs, and procedures (TTPs) alongside with collecting Indicators of Compromise (IOCs) is an valuable to successfully configuring security methods for protection.
What is ANY.RUN?
ANY.RUN is a cloud-based malware sandbox designed to expedite likelihood evaluation for security teams, utilizing YARA ideas and Suricata for instantaneous malware detection (around 40 seconds) and computerized family identification.
Unlike utterly computerized alternate ideas, ANY.RUN presents precise-time interaction with the virtual machine by a browser interface, which is an valuable for countering zero-day exploits and developed malware that will maybe bypass signature-based detection.
ANY.RUN’s cloud-based nature also eliminates setup and maintenance burdens for DevOps teams, making it imprint-efficient for corporations.
The intuitive interface is neatly-suited for onboarding contemporary security personnel, allowing even junior analysts to abruptly rob malware evaluation and extract Indicators of Compromise (IOCs).
Are you from SOC and DFIR Groups? â Analyse Malware Incidents & procure dwell Procure admission to with ANY.RUN -> Delivery up Now for Free.
Source credit : cybersecuritynews.com