New macOS Adload Malware Bypasses Built-in macOS Antivirus Detection
.webp)
A brand recent variant of the infamous Adload malware has been stumbled on to circumvent the most up-to-date updates to Apple’s built-in antivirus, XProtect.
No subject Apple’s efforts to enhance its defenses with a significant substitute to its malware signature checklist, Adload’s authors obtain impulsively tailored, rendering these recent measures ineffective in opposition to the most up-to-date iterations of the malware.

Apple’s Broad Adload Signature Update
Apple’s security crew neutral recently applied a appreciable substitute to XProtect, adding 74 recent guidelines in version 2192 and 10 additional guidelines in version 2193, released on April thirtieth.
This substitute aimed to fight the Adload spyware and adware, which has been a continual threat to macOS devices.
Integrate ANY.RUN in Your Company for Effective Malware Diagnosis
Are you from SOC, Threat Study, or DFIR departments? If that is the case, you perchance can join an on-line neighborhood of 400,000 neutral security researchers:
- Staunch-time Detection
- Interactive Malware Diagnosis
- Easy to Be taught by New Security Crew individuals
- Rep detailed experiences with maximum recordsdata
- Save Up Virtual Machine in Linux & all Windows OS Versions
- Work on the side of Malware Safely
In uncover for you to test all these components now with fully free entry to the sandbox:
Per the recent story by SentinelOne, a recent stress of Adload malware has been stumbled on that’s able to bypassing the built-in antivirus detection of macOS, posing a significant threat to the safety of Mac programs.
Forward of this substitute, XProtect had 207 guidelines, of which a significant piece centered historical versions of Adload.
The factitious marked a 24% lengthen within the rule count, showcasing Apple’s dedication to combating this pervasive spyware and adware.
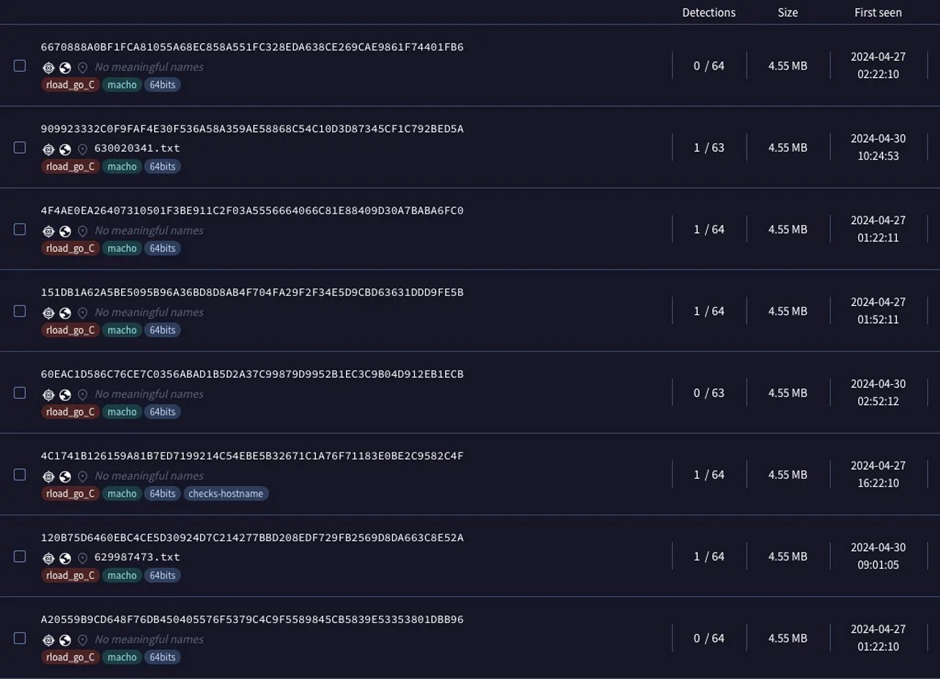
No subject these efforts, recent versions of Adload had been identified, evading detection by every XProtect and other antivirus engines on VirusTotal.
This trend underscores malware authors’ adaptability and the challenges confronted by security teams in protecting up with evolving threats.
The most modern Adload samples obtain shown an alarming skill to circumvent detection mechanisms. Before all the issues, varied antivirus engines detected many of those samples.
On the alternative hand, because the week improved, samples began to floor that eluded XProtect and other vendors’ detection on VirusTotal.
This evasion highlights the sophistication of the recent Adload variants and the want for continuous vigilance and updates from security companies.
New Adload Sprint Variant (Reload/Lador)
Among the recent variants, one in pronounce, compiled completely for the Intel x86_64 structure, has demonstrated a shut to-total detection evasion, with 0 or highest 1 detection among VirusTotal engines.
This variant acts as an initial dropper for the next stage payload, without a clear guardian executable, application, or disk image, suggesting a distribution thru cracked or trojanized apps.
The samples noticed embed a different custom domain, following identified Adload patterns, indicating a stylish and organized distribution components.
| SHA1 | Arena |
| 13312b3dad9633fa185351e28397c21415d95125 | api[.]deployquest[.]com |
| 21c447cac1c13a6804e52f216a4c41a20c963c01 | api[.]searchwebmesh[.]com |
| 5b1d60c6f461cd8ba91cbca5c7190f4b2752979d | api[.]generalmodules[.]com |
| 67a56aa269b9301981c0538ace75bec2cd381656 | api[.]validexplorer[.]com |
| 7aaff54d2d6e3f38e51a4f084e17b9aad79a9de0 | api[.]operativeeng[.]com |
| 912a2ab06d3afe89e8e2ad19d3300055f0e0a968 | api[.]buffermanager[.]com |
| a99d03fc3b32742de6688274a3ee3cdaef0172bf | api[.]lookwebresults[.]com |
| f166eb63162ce4a5ac169e01c160be98b0e27e13 | api[.]navigationbuffer[.]com |
| feb2c674f135410c3ced05c301f19ab461e37b20 | api[.]inetprogress[.]com |
Upon execution, these droppers abolish diagram recordsdata discovery by ability of the ioreg utility:
ioreg -rd1 -c IOPlatformExpertDevice
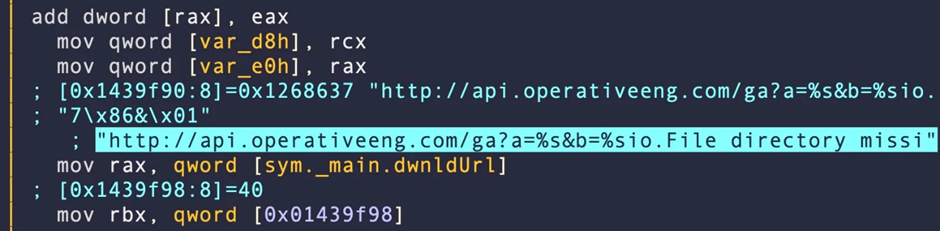
The malware then seeks to resolve a hardcoded domain name, sym._main.dwnldUrl, and sends an http question to retrieve a a lot-off gzip.
Minor Tweak Evades XProtect Signature Rule
A more in-depth examination of the binaries finds that no subject Apple’s centered efforts, the malware authors obtain managed to evade detection by making minor changes, corresponding to replacing the string main.DownloadURL with main.dwnldUrl.
rule macos_smolgolf_adload_dropper { meta: description = "MACOS.ADLOAD" strings: $varName = "main.DownloadURL" $libraryName = "github.com/denisbrodbeck/machineid.ID" $execCommand = "os/exec.Command" condition: Macho and all of them }This subtle commerce has allowed the most up-to-date Adload samples to scamper past XProtect’s defenses, underscoring the continuing cat-and-mouse recreation between malware authors and security teams.
As the battle in opposition to malware like Adload continues, it’s obvious that reliance on built-in antivirus solutions by myself may per chance well no longer suffice.
Enterprises and particular person customers are inspired to acquire in mind third-celebration security solutions to keep in mind toddle comprehensive security in opposition to those and other subtle threats.
For those inquisitive about the safety of their macOS devices, exploring additional safety features and staying told about the most up-to-date threats and detection strategies is more the biggest than ever.
Source credit : cybersecuritynews.com

