[ad_1]

As many as 10 security flaws have been uncovered in Google’s Quick Share data transfer utility for Android and Windows that could be assembled to trigger remote code execution (RCE) chain on systems that have the software installed.
“The Quick Share application implements its own specific application-layer communication protocol to support file transfers between nearby, compatible devices,” SafeBreach Labs researchers Or Yair and Shmuel Cohen said in a technical report shared with The Hacker News.
“By investigating how the protocol works, we were able to fuzz and identify logic within the Quick Share application for Windows that we could manipulate or bypass.”
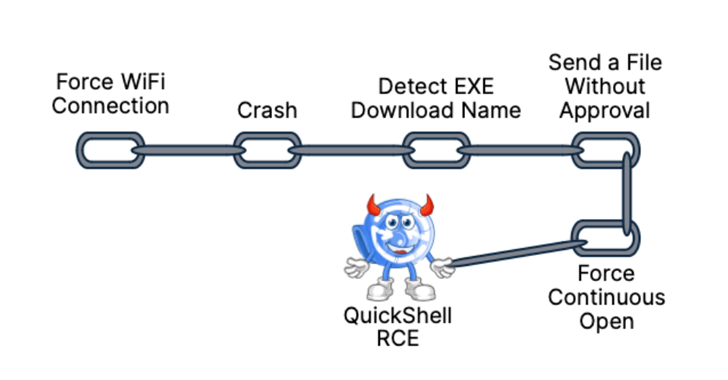
The result is the discovery of 10 vulnerabilities – nine affecting Quick Share for Windows and one impacting Android – that could be fashioned into an “innovative and unconventional” RCE attack chain to run arbitrary code on Windows hosts. The RCE attack chain has been codenamed QuickShell.

The shortcomings span six remote denial-of-service (DoS) flaws, two unauthorized files write bugs each identified in Android and Windows versions of the software, one directory traversal, and one case of forced Wi-Fi connection.
The issues have been addressed in Quick Share version 1.0.1724.0 and later. Google is collectively tracking the flaws under the below two CVE identifiers –
- CVE-2024-38271 (CVSS score: 5.9) – A vulnerability that forces a victim to stay connected to a temporary Wi-Fi connection created for sharing
- CVE-2024-38272 (CVSS score: 7.1) – A vulnerability that allows an attacker to bypass the accept file dialog on Windows
Quick Share, formerly Nearby Share, is a peer-to-peer file-sharing utility that allows users to transfer photos, videos, documents, audio files or entire folders between Android devices, Chromebooks, and Windows desktops and laptops in close proximity. Both devices must be within 5 m (16 feet) of each other with Bluetooth and Wi-Fi enabled.
In a nutshell, the identified shortcomings could be used to remotely write files into devices without approval, force the Windows app to crash, redirect its traffic to a Wi-Fi access point under an attacker’s control, and traverse paths to the user’s folder.

But more importantly, the researchers found that the ability to force the target device into connecting to a different Wi-Fi network and create files in the Downloads folder could be combined to initiate a chain of steps that ultimately lead to remote code execution.
The findings, first presented at DEF CON 32 today, are a culmination of a deeper analysis of the Protobuf-based proprietary protocol and the logic that undergirds the system. They are significant not least because they highlight how seemingly harmless known issues could open the door to a successful compromise and could pose serious risks when combined with other flaws.
“This research reveals the security challenges introduced by the complexity of a data-transfer utility attempting to support so many communication protocols and devices,” SafeBreach Labs said in a statement. “It also underscores the critical security risks that can be created by chaining seemingly low-risk, known, or unfixed vulnerabilities together.”
[ad_2]