RTM Locker Ransomware Attacks Linux, NAS, and ESXi Servers

The RTM Locker ransomware gang has been stumbled on to use a Linux encryptor that focuses explicitly on virtual machines on VMware ESXi servers, making it the most smartly-liked occasion of an endeavor-oriented ransomware attack.
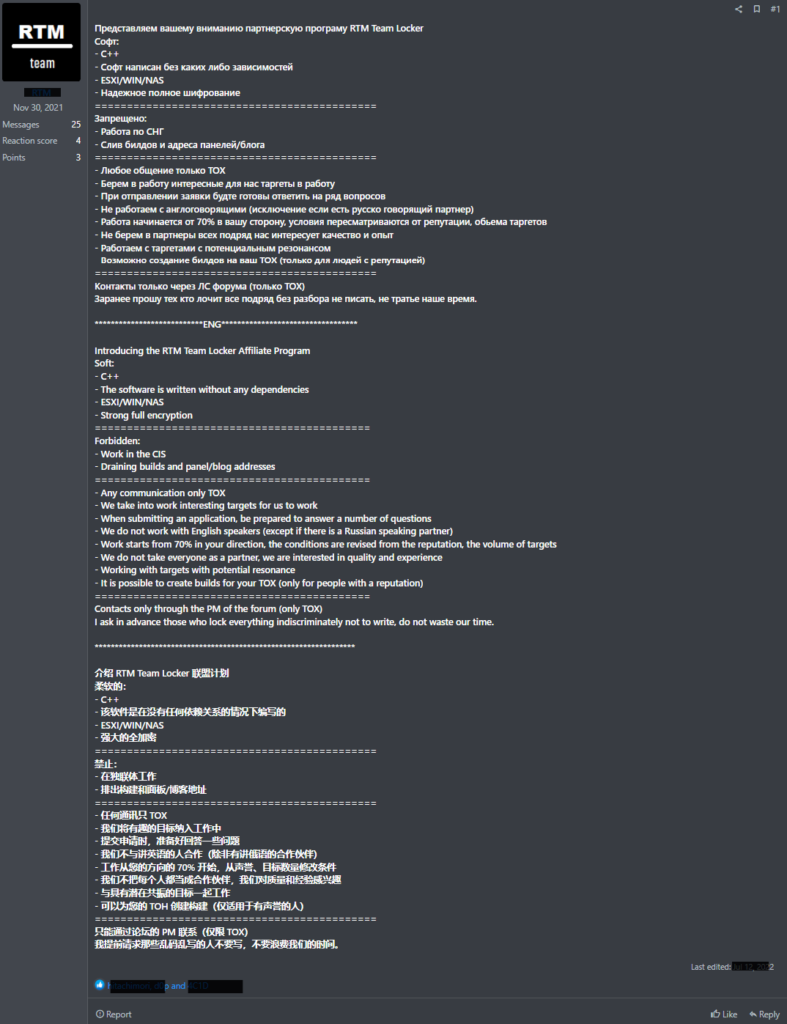
Uptycs’ Threat Intelligence unit uncovered the RTM Locker risk faction whereas conducting darkish net reconnaissance.
Since 2015, the RTM cybercrime team has been angry by financial fraud, the utilize of a personalised-made banking trojan to steal money from their targets.
Trellix cybersecurity agency and Uptycs neutral not too lengthy ago revealed that RTM Locker initiated a fresh Ransomware-as-a-Carrier (RaaS) endeavor, actively hiring mates, including ex-Conti cybercriminals.
Technical Evaluation
RTM Locker and Babuk ransomware allotment commonalities, such as ECDH Curve25519 for asymmetric encryption and random number technology.
On the replace hand, Babuk makes utilize of sosemanuk, whereas RTM Locker makes utilize of ChaCha20 for asymmetric encryption, which differentiates the 2.
Upon preliminary inspection of the ransomware binary, it became apparent that this system become once tailor-made towards ESXi due to two ESXi commands initially set aside of the code.
The binary is statically compiled and stripped, which enables it to scramble on diverse systems and makes reverse engineering a appealing project.
Moreover, the preliminary come by admission to vector stays unknown, including a layer of complexity to the scenario.
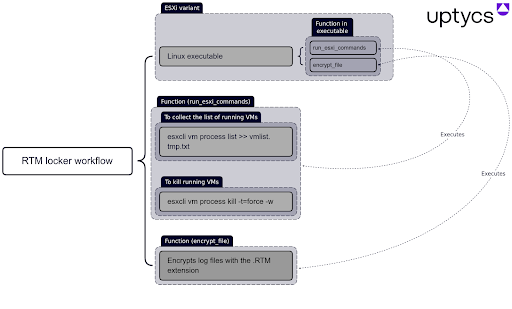
Whereas on this binary, a actually worthy capabilities are:-
- name_threads
- run_esxi_commands
- pthread_wrapper_main
Here underneath, now we comprise mentioned the 2 ESXi commands which could perhaps perhaps be scramble the utilize of this program:-
- esxcli vm process checklist >> vmlist.tmp.txt: This disclose lists the total ESXi VMs currently operating on the system.
- esxcli vm process abolish -t=power -w: This disclose kills the total ESXi VMs that were stumbled on by the previous disclose.
Due to give a boost to oversight capabilities and superior helpful resource administration, agencies comprise migrated to virtual machines (VMs) in fresh years.
This outcomes in organizations usually utilizing devoted devices and VMware ESXi servers net house hosting a pair of virtual servers to handle their infrastructure.
Following this trend, ransomware operations comprise developed Linux encryptors tailor-made to targeting ESXi servers, which can comprehensively encrypt all endeavor recordsdata.
Moreover, the RTM Locker Linux encryptor appears to be designed explicitly for assaulting VMware ESXi systems, given the a range of references to commands employed in VM administration.
Ransom Repeat
As phase of its file encryption routine, the encryptor modifies the names of the affected recordsdata by appending the “.RTM” extension.
Following the completion of the encryption process, the malware proceeds to generate ransom notes on the compromised system, which could perhaps perhaps be usually labeled as:-
- “!!! Warning !!!”
After encrypting the sufferer’s recordsdata and appending the “.RTM” extension to their names, the ransom notes issued by the attackers usually glean threats to post the stolen recordsdata if the sufferer fails to pay a ransom.
These notes also command the sufferer to contact RTM’s “enhance” within 48 hours by the utilization of the anonymous messaging platform Tox to initiate negotiations for the ransom price.
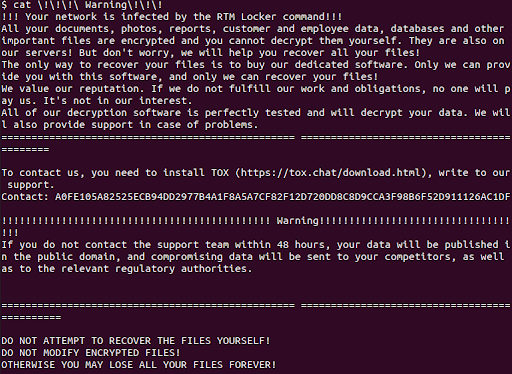
Traditionally, RTM Locker relied on TOR price negotiation sites to talk with victims and question ransom funds.
On the replace hand, the attackers comprise neutral not too lengthy ago shifted their dialog strategy and begun the utilize of the anonymous messaging platform TOX.
The come and deployment of an ESXi-targeting variant of the RTM Locker ransomware indicate that this risk actor poses a critical risk to endeavor-stage organizations.
Source credit : cybersecuritynews.com


