U.S. Sanctions Cybercrime Network Behind Massive Residential Proxy Bothnet Service
.webp)
The United States has imposed sanctions on a cybercrime network accountable for working an enormous residential proxy botnet service to strive in opposition to cybercrime.
This network, 911.re, has been implicated in lots of illicit actions. It leverages residential IP addresses to anonymize malicious visitors and evade detection.

The 911.re Network
The 911.re service, a Residential Proxies As A Provider (RPAAS) platform, has been operational since early 2018.
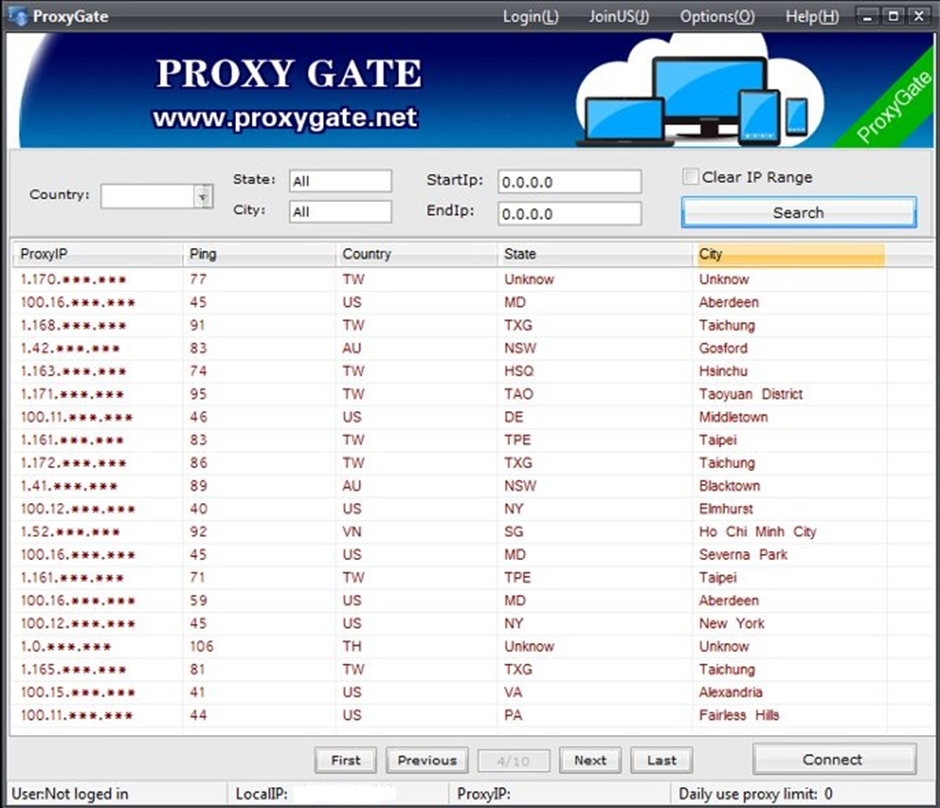
Per the U.S. DEPARTMENT OF THE TREASURY experiences, It permits customers to rent residential IP addresses, making their web visitors seem as if it originates from legit residential customers.
While such companies and products will even be dilapidated for legit purposes worship market surveys and Web optimization, additionally they provide a quilt for legal actions, making it subtle to hint malicious visitors abet to its supply.

A total study project, initiated in January 2021, uncovered the extensive infrastructure of the 911.re network.
The study printed that 911. operates without vetting or verification, allowing someone to rent residential nodes.
The network comprises over 120,000 residential proxy nodes disbursed globally, with distinguished concentrations in the US, South Korea, Peru, and Japan.
The 911.re network recruits residential nodes thru two free VPN companies and products, Veil VPN and Dew VPN.
These applications, which seem legit, install utility on customers’ computer programs that connect them to the 911.re network without their informed consent.
The contaminated nodes protect a continual TCP connection to notify-and-alter (C2) servers, making them available for use by 911.re purchasers.
The study highlighted lots of vulnerabilities and seemingly exploits associated to the 911.re network.
These contain:
- IP Filtering-Basically basically based Provider Exploits: 911. re-customers can web proper of entry to ISP customer companies and products and doubtlessly fracture confidential recordsdata by masquerading because the residential proxy proprietor.
- Lateral Lumber Assaults: The infection permits 911.re customers to web proper of entry to shared resources on the native network and probe the LAN network of the contaminated node.
- DNS Router Cache Poisoning: Attackers can poison the DNS cache of the LAN router, enabling extra attacks.
The operation of the 911.re network raises distinguished proper and moral concerns.
Residential node owners, on the whole blind to their participation, could per chance per chance face legal or civil authorized responsibility if their computer programs are dilapidated for malicious actions.
The dearth of informed consent and the potential for severe proper consequences underscore the necessity for stricter regulations and oversight of such companies and products.
Per these findings, the U.S. authorities has imposed sanctions on the entities in the abet of the 911.re network.
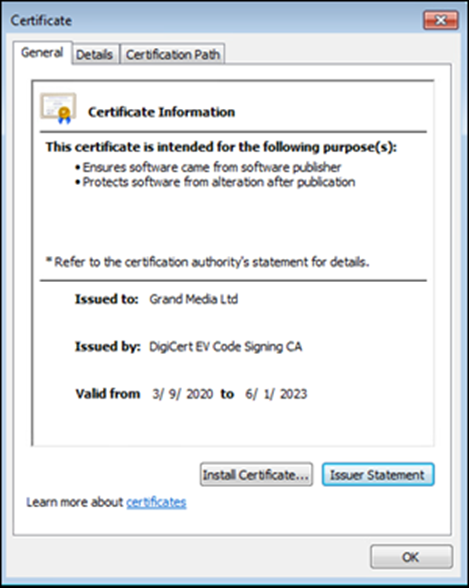
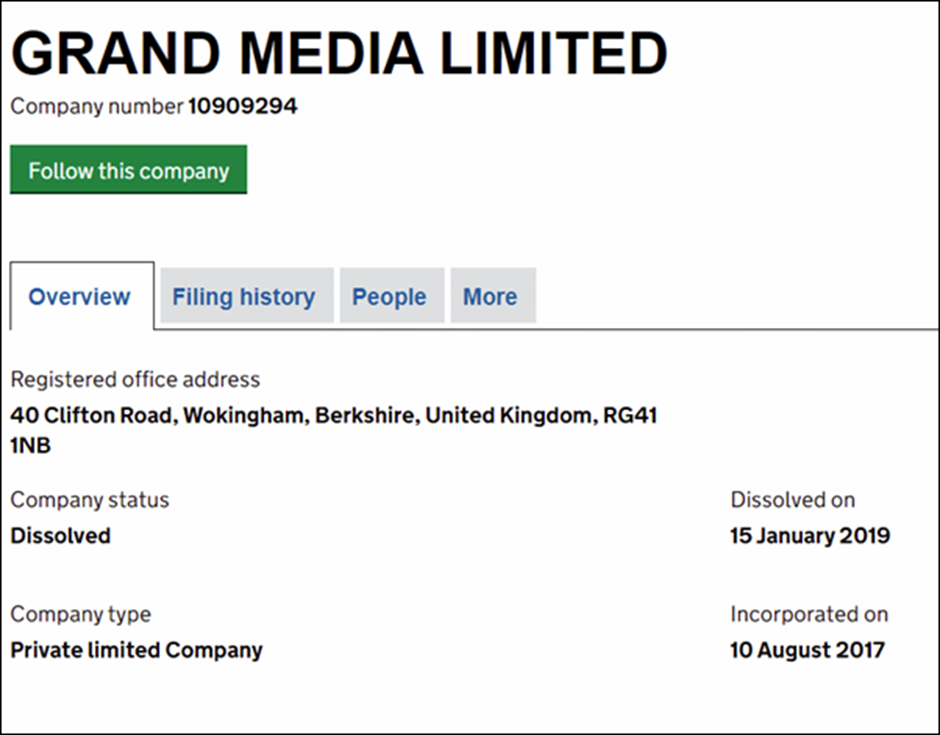
The sanctions target the shell companies Global Media Ltd and Immense Media Ltd, which could per chance per chance be dilapidated to stamp the binaries for Veil VPN and Dew VPN.
These measures purpose to disrupt the operations of the 911.re network and protect its operators accountable for his or her role in facilitating cybercrime.

The invention and exposure of the 911.re network highlights the rising menace of residential proxy botnets in the cybercrime landscape.
The U.S. sanctions signify a a will must bring together step in combating this menace and holding folk and organizations from the hazards associated to such companies and products.
Further study and world cooperation are very fundamental to handle the network’s plump extent and forestall future a similar threats.
Indicators of compromise (IOCs)
Binaries ·Maskvpn.exe (2/68 virus total) MD5: a220528f31dceddc955b791b13ac4989 SHA-1: 57a83b83a11b6e27c9e88a7835d8a84744d79bdd SHA-256: e801fa187027537337d8b4e4bde3a7da95499172f6b1477830a216d0a385518b ·Dewvpn.exe (1/67 virus total) MD5: 12059484a8951a8356c60c46f659a35e SHA1: 3916aeaa61a6e97d6c1746b18c05fd77584de5d8 SHA256: daa21c58a1ace38d1eebcda6fef3502fa3492ccf09fbccfa6ce103c9222d9afc ·maskvpn-setup.exe (2/68 virus total) MD5: f9634d85ca0138cfddfe6e58fa1c6160 SHA1: 5ffa0b96b7257d804beddb87b0a21e871a1296b4 SHA256: 1013eb0e3dbbc16c8b6d0659cca46a084e767b2d9bb8e498e07016bfdb978780 ·mask_svc.exe (1/67 virus total) MD5: c6b1934d3e588271f27a38bfeed42abb SHA1:08072ecb9042e6f7383d118c78d45b42a418864f SHA256: 35ec7f4d10493f28d582440719e6f622d9a2a102e40a0bc7c4924a3635a7f5a8 DewVPN-Setup.exe (1/67 virus total) MD5: 8e8b072c93246808a7f24554ca593c59 SHA1: d06418cacd11e25af37a41724d55dffc24d6fe5b SHA256: f422a38d72785c402948c94ae81336383a9fd48167272f29cdc434ce7e51e02b dew_svc.exe (0/69 virus total) MD5: 5feb35a7186a5be50b7aa158866b8aa3 SHA1:c0c7e272f3e48d8dfe559aa5f63ad3a46c76fb9e SHA256: a8e72d202f9a83e6bdfd03a822fae6d4ee2d4b35a6f73a06e9d59e2e49b3070aDNS queries:
. vpn[.]maskvpn[.]org · user[.]maskvpn[.]org · net[.]dewvpn[.]com · wan[.]dewvpn[.]net · connect[.]dewvpn[.]ccIPv4:
98.126.176.51 · 98.126.176.52 · 98.126.176.53 · 67.198.169.2 · 98.126.244.26 · 98.126.13.146 · 174.139.80.66 · 67.229.60.114 · 174.139.78.106 · 98.126.1.130 · 174.139.100.202 · 67.198.134.186 · 98.126.5.106 Outgoing TCP ports used by Mask VPN and Dew VPN to initiate persistent C2 communications · 441 TCP · 430 TCP · 433 TCP · 434 TCP · 436 TCP · 440 TCP · 439 TCP · 435 TCP · 428 TCP · 432 TCP · 438 TCPSource credit : cybersecuritynews.com
