Savvy Seahorse Hackers Leverage DNS CNAME Records to Exploit Victims

Cybersecurity researchers unveiled a cosmopolitan rip-off operation, “Savvy Seahorse,” exploiting victims by evolved DNS manipulation techniques.
This operation, active since no longer lower than August 2021, has flown below the radar by leveraging DNS canonical title (CNAME) recordsdata to make a dynamic and elusive site visitors distribution system (TDS) for monetary rip-off campaigns.

A Fresh Come to Cybercrime
Savvy Seahorse’s campaigns are no longer your frequent phishing attempts. They incorporate spurious ChatGPT and WhatsApp bots that provide computerized responses, luring victims into providing interior most recordsdata below the guise of excessive-return funding opportunities.
These campaigns plan a huge desire of language audio system, along with Russian, Polish, Italian, German, Czech, Turkish, French, Spanish, and English, while excluding doable victims in Ukraine and some other countries.
The crux of Savvy Seahorse’s procedure lies in abusing the Domain Name System (DNS).
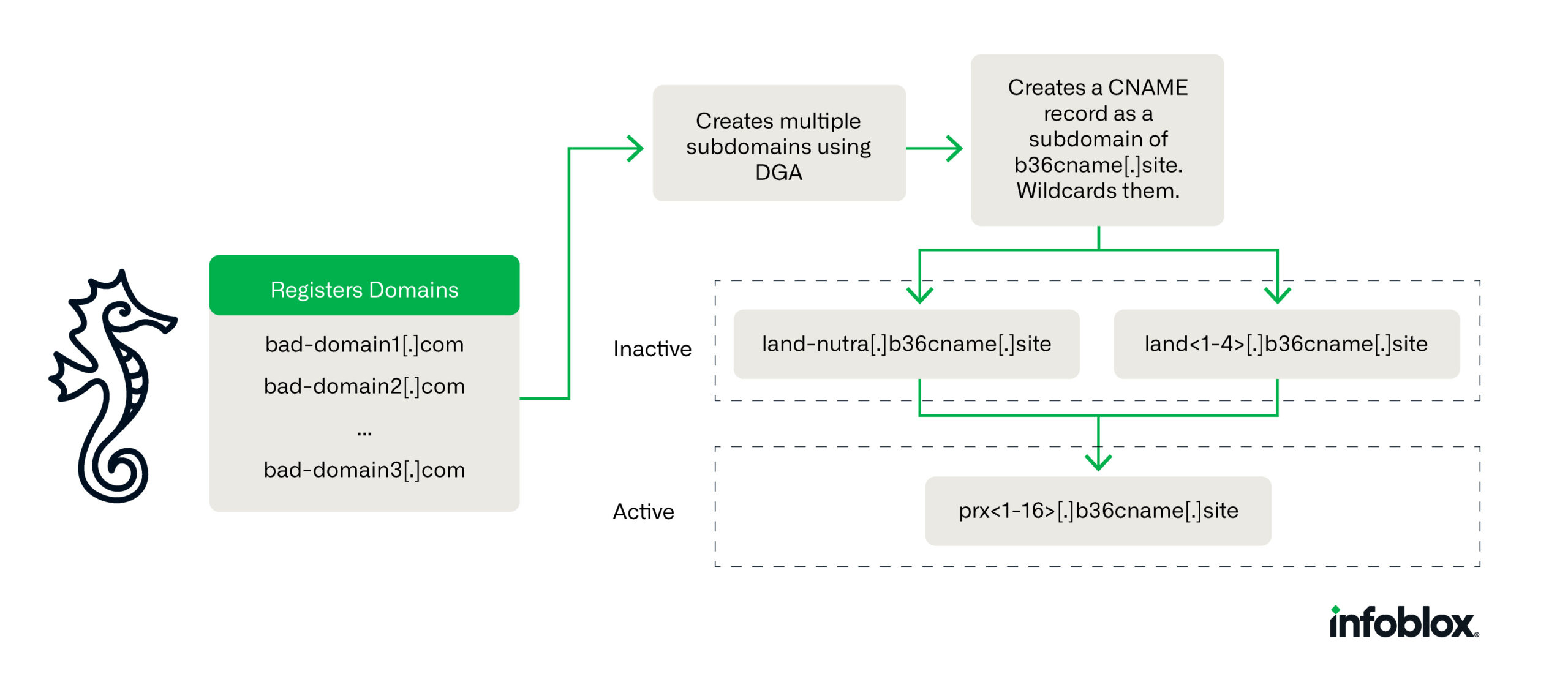
By leveraging CNAME recordsdata, the threat actor has developed a cosmopolitan TDS that enables for dynamic declare provide and IP address updates, making their malicious campaigns essential to detect and shut down, infoblox researchers stated.
This procedure has enabled Savvy Seahorse to evade detection by the safety alternate, marking the first reported use of CNAMEs for such malicious functions.
Delicate Scam Operations
Savvy Seahorse’s operations are meticulously planned and performed. The campaigns are primarily delivered by Facebook commercials, enticing victims to spurious funding platforms.
Once there, victims are tricked into funding their accounts with the promise of broad returns.
The utilization of dedicated web web hosting and conventional IP address modifications, coupled with immediate-lived particular particular person campaigns, makes tracking and combating these operations a fearless snort.
The operation’s infrastructure is spacious, with approximately 4.2k snide domains linked by a single CNAME file to a subdomain of b36cname[.]dwelling.
This setup permits Savvy Seahorse to rapid make self sustaining campaigns, complicating passive DNS (pDNS) diagnosis and evading detection efforts, reads infoblox file.
The Role of CNAME in Cybersecurity
Utilizing CNAME recordsdata for malicious functions highlights a indispensable oversight within the cybersecurity alternate’s figuring out of DNS’s role in cybercrime.
CNAME recordsdata, which scheme one enviornment title to 1 more, are a classic allotment of DNS that may perhaps be exploited to comprise watch over a spacious, shifting workforce of malicious domains successfully.
This procedure permits Savvy Seahorse to scale and transfer operations with out note, presenting a fascinating plan for cybersecurity defenses.
Implications and Protection Solutions
The invention of Savvy Seahorse’s operations underscores the need for the cybersecurity workforce to reassess the role of DNS in cybercrime.
By figuring out the techniques, techniques, and procedures employed by threat actors fancy Savvy Seahorse, cybersecurity experts can function extra perfect solutions to detect and disrupt such operations.
Blocking the snide enviornment to which the CNAME recordsdata point most continuously is a easy but perfect skill to mitigating the threat posed by this and identical operations.
In conclusion, the Savvy Seahorse marketing campaign represents a indispensable evolution in cybercriminal techniques, leveraging DNS in ways previously unrecognized by the safety alternate.
As cybersecurity experts work to counter these sophisticated threats, the importance of continuous study and adaptation in cybersecurity solutions has in no plan been extra evident.
That you may perhaps well block malware, along with Trojans, ransomware, adware, rootkits, worms, and nil-day exploits, with Perimeter81 malware security. All are extraordinarily detrimental, can wreak havoc, and rupture your network.
Now not sleep up to now on Cybersecurity recordsdata, Whitepapers, and Infographics. Apply us on LinkedIn & Twitter.
Source credit : cybersecuritynews.com


