Top 11 Open Source Cloud Security Tools 2024

Introduction :
By seeing the heading of this article, that you just may well presumably be wondering what’s all about open provide cloud.
It’s a carrier or acknowledge which bought developed by utilizing open-provide instrument and expertise.

These Cloud Safety Instruments are precious for any public and non-public units like SaaS, PaaS, DaaS, and heaps others.
Here’s completely built and operates by open-provide technologies.
In on the present time’s world, 83 p.c of enterprises keep their workload to the open-provide cloud to obtain the exact recordsdata with low rate and time.
It’s cheap for every alternate and employer.
This instrument adoption can present a steal to interoperability.
Now let us focus on about open-provide cloud security, which measures and configures to guard the cloud recordsdata.
It additionally protects customers’ privacy to boot to sets the authentication principles for all particular person devices and users.
It additionally helps to filter the web site online visitors where that you just will be in a assign to configure cloud security to obtain the yelp wishes of your alternate.
These Cybersecurity tools rep a natty market share where they’ll meet the requirement of project-grade security instrument. Many open provide security tools accessible on the market can work like the paid ones. Whenever that you just may well presumably be fresh within the alternate, that you just will be in a assign to open your alternate utilizing the free version.
Many runt and mid-size enterprises combine the free and paid open-provide Cloud Safety tools to increase their organization and provide protection to their community and digital sources.
Here we are succesful of focus on about the list of open-provide cloud security tools that support your organization safe from hackers.
What’s open provide security Utility?
open provide cloud security tools are very scalable, versatile, rate-efficient, and successful.
Many kinds of cloud computing utilize open-provide instrument, and on-line teams serve it up, which makes clear it’s reputable and just.
Table of Contents
What’s open provide security Utility?
High 11 Inaugurate Source Cloud Safety Instruments 2024
1.Wazuh
2.Osquery
3.GoAudit
4.Grapl
5.OSSEC
6.Suricata
7.Zeek/Bro
8.Panther
9.Kali Linux
10.KeePass
11.Safety Monkey
High 11 Inaugurate Source Cloud Safety Instruments Substances
Closing Thoughts
Additionally Read
High 11 Inaugurate Source Cloud Safety Instruments 2024
- Wazuh
- Osquery
- GoAudit
- Grapl
- Safety Monkey
- Suricata
- Zeek/Bro
- Panther
- Kali Linux
- KeePass
- pacbot
- OSSEC
High 11 Inaugurate Source Cloud Safety Instruments Substances
| High 11 Inaugurate Source Cloud Safety Instruments | Substances |
|---|---|
| 1. Wazuh | 1. Log Management 2. Intrusion Detection Machine (IDS) 3. File Integrity Monitoring (FIM) 4. Vulnerability Detection 5.Monitoring and alerts in exact time |
| 2. Osquery | 1. Infamous-Platform Pork up 2. Querying Machine Narrate 3. Accurate-Time Monitoring 4. Logging and Auditing 5.Searching on the job and sockets |
| 3. GoAudit | 1. Integration with Linux Audit Subsystem 2. Audit Event Generation 3. Rule Configuration 4. Accurate-time Auditing |
| 4. Grapl | 1. Graph-Based Diagnosis 2. Cloud-Native Architecture 3. Recordsdata Ingestion 4. Threat Detection and Trying 5.Correlating events and sending alerts |
| 5. Safety Monkey | 1. Cloud Provider Pork up 2. Configuration Monitoring 3. Accurate-Time Alerting 4. Compliance Monitoring 5.Configuration and security policy prognosis |
| 6. Suricata | 1.Community Traffic Diagnosis 2. Signature-Based Detection 3. Protocol Diagnosis 4. Multi-Threading and Performance 5.Extra than one chance intelligence feed integration |
| 7. Zeek/Bro | 1. Accurate-Time Community Monitoring 2. Protocol Diagnosis 3. Traffic Inspection and Metadata Extraction 4. Intrusion Detection 5.Helps lickety-split packet processing |
| 8. Panther | 1. Log Series and Diagnosis 2. Accurate-time Monitoring and Alerting 3. Compliance Monitoring 4. Infrastructure as Code (IaC) Safety 5.Pre-built queries and detection principles |
| 9. Kali Linux | 1. Exploit Instruments 2. Vulnerability Overview 3. Wireless Community Finding out 4. Password Cracking 5.Privacy and anonymity tools |
| 10. PacBot | 1. Continuous Compliance Monitoring 2. Computerized Compliance Assessments 3. Coverage-Based Compliance Framework 4. Remediation Workflow 5.Scalability for natty deployments |
| 11. OSSEC | 1. Log Diagnosis 2. File Integrity Monitoring (FIM) 3. Intrusion Detection 4. Active Response 5.Finding rootkits and taking action |
1. Wazuh
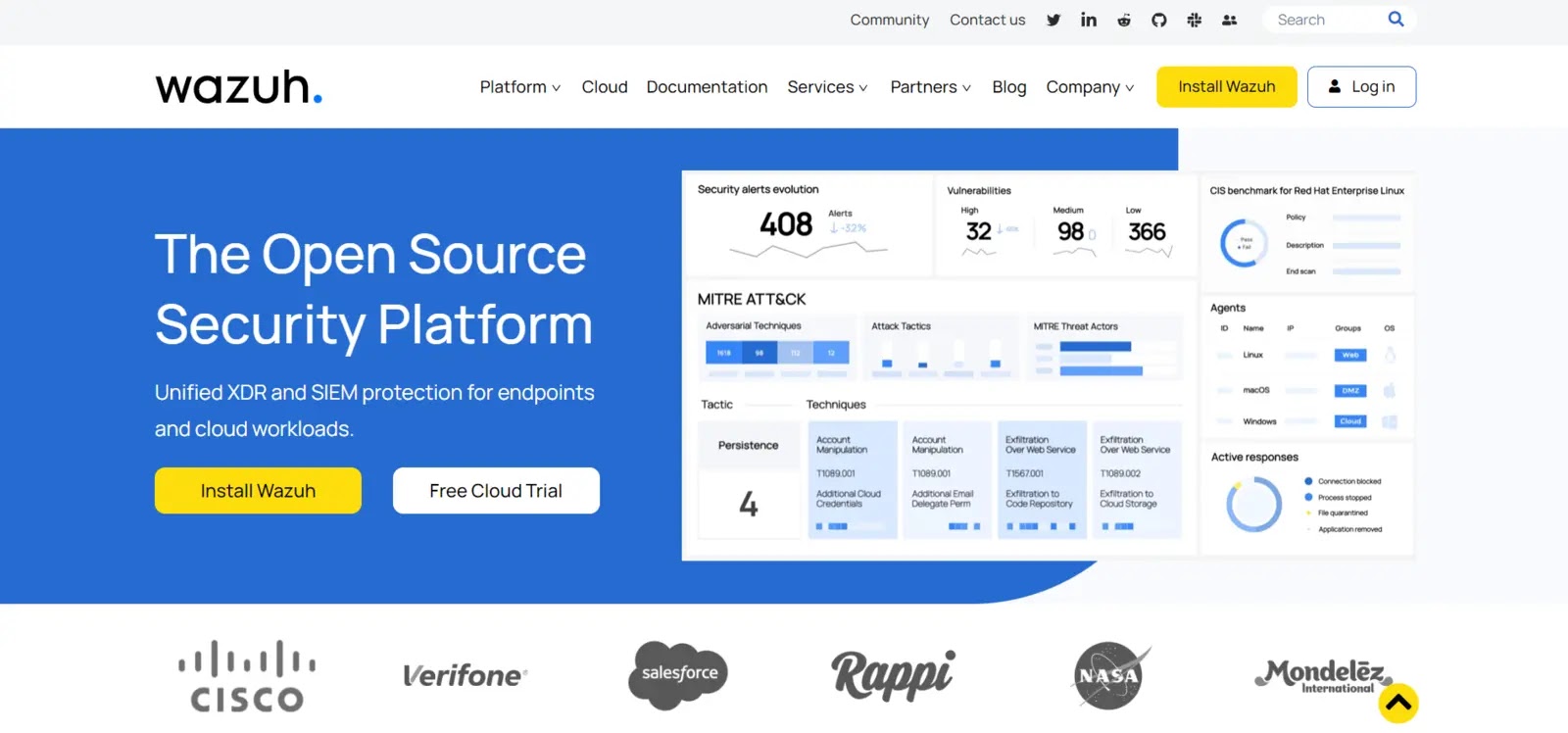
Wazuh is an all-inclusive cybersecurity platform alongside with SIEM, HIDS, and XDR aspects.
Wazuh’s open-provide ethos has helped it originate a with out warning growing user community where it may probably perchance present first-rate customer carrier and solicit suggestions and suggestions for enchancment.
Over 200k companies, alongside with heaps of the Fortune 100, utilize Wazuh.
Wazuh has two deployment alternate options for its solutions: on-premises and the cloud-based Wazuh Cloud, which aspects a highly scalable and adaptable infrastructure.
Search recordsdata from the vitality of Wazuh Cloud by placing in Wazuh or signing up for a free trial now!
Substances
- We utilize OSSEC, an open-provide intrusion detection machine, to video display host exercise, detect intrusions, and alert users.
- It detects tampering and malware by monitoring necessary machine files and directories.
- It checks file and directory changes for illegal changes to detect intrusions and malware.
- This analyzes machine files and folders for habitual changes to detect malware or interference.
| What’s Staunch? | What will likely be Better? |
|---|---|
| Log Diagnosis and Monitoring | Plugins or customization may well also just be wanted for some aspects. |
| Intrusion Detection and Prevention | Dependence on timely security updates and fixes. |
| File Integrity Monitoring | |
| Threat Intelligence Integration |
2. Osquery
.webp)
This free monitoring instrument uses SQL to operate.
It’s acceptable with Home windows, macOS, Linux, FreeBSD, and extra.
This gives aesthetic performance and opens up the working machine.
It additionally works well with SQL-based queries, yielding exact recordsdata on issues like currently active processes, community connections, hardware events, browser plugins, and heaps others.
Here’s begun in 2014 and changed into established by Facebook. Low-level behavior changed into maintained after utilizing this carrier.
These engineers rep discovered this expertise to be precious, they in most cases’re making exact utilize of it.
That you too can set up Osquery to detect unknown malware and get alerts if a chance is detected.
Substances
- Other folk can utilize SQL-based inquire language to discuss with with the OS by Osquery.
- It must always video display the working machine with out spoil for particular events.
- Osquery streams log recordsdata from loads of programs. Machine, security, utility, and custom log files are sources.
- It must always detect hacked or malicious hosts.
| What’s Staunch? | What will likely be Better? |
|---|---|
| Infamous-Platform Pork up | Need fixed monitoring and optimization to shield away from overload. |
| Accurate-Time Visibility | Build a question to Performance and Scalability |
| Threat Detection and Incident Response | |
| Compliance Monitoring |
3. GoAudit
The Linux Audit machine contains two aspects: the kernel instrument and the monitoring syscalls.
This 2d one is the user-space daemon which is guilty for audit writing, and it additionally records.
After its 2016 liberate, improvements in logging for multiline events and prognosis of JSON Blob had been apparent.
This lets you rep a Netlink conversation with the kernel straight.
Any attainable dangers to your company will even be filtered out.
It’s no longer exact the correct security measure; it’s additionally a helpful instrument for solving any sequence of considerations.
It’s reputable and efficient, so budge ahead and use it.
Substances
- GoAudit lets you test the machine calls that Linux processes create.
- It must always test the machine calls that Linux processes create.
- This can support video display of events that happen on a community, like hyperlinks, socket operations, and community packet filtering.
- It must always support video display of events that happen on a community, like hyperlinks, socket operations, and community packet filtering.
| What’s Staunch? | What will likely be better? |
|---|---|
| Granular Event Auditing | Documentation and Sources |
| Accurate-Time Monitoring | Evolved Alerting and Notifications |
| Entire Logging | |
| Configurable Audit Principles |
4. Grapl
This changed into launched the final year in March, and it’s a Graph Analytics Platform that’s perfect for detection, incident response, and forensics.
It deduces the attacker’s motivation and responds defensively accordingly.
It protects the community in indispensable the identical intention as a natural defender would, utilizing a graph-based intention and an consciousness of the community’s fats extent.
Grapl is consistently processing the safety-associated logs, which aids in their transformation correct into a subgraph.
It marges the subgraphs into Master Graph so as that it may probably perchance think the action across the atmosphere.
It executes the analyzers where any suspicious sample appears to be like, it bought discovered within the scry subgraph.
After that, Grapl begins his inquiry.
Substances
- Graph units and analyzes host, job, community online page online visitors, and user anecdote interactions utilizing a graph database.
- Grapl uses rule-based, anomaly-based, and machine-learning algorithms to detect security considerations and habitual behavior.
- It enables security teams to video display and evaluate security occurrences in exact-time.
- It gives incident investigation and forensics tools.
| What’s Staunch ? | What will likely be Better? |
|---|---|
| Graph Diagnosis | Ease of Deployment and Configuration |
| Scalability and Performance | Documentation and Community Pork up |
| Computerized Threat Detection | |
| Extensibility and Customization |
5. Safety Monkey

One more instrument for monitoring AWS, GCP, and OpenStack policy changes and inclined settings.
Netflix developed the instrument to repeat customers of apprehensive configurations and present a single UI to browse and search all accounts, territories, and cloud products and providers.
The instrument can additionally beef up custom anecdote kinds, watchers, auditors, and alerts.
Substances
- Safety Monkey displays digital machines, storage buckets, security teams, and database cases.
- It uses Nessus, AWS Inspector, and other vulnerability trying out tools.
- It displays cloud infrastructure changes and informs straight within the occasion that they’re unauthorized or unexpected.
- This security Monkey creates and implements security policies and compliance units.
| What’s Staunch? | What will likely be Better? |
|---|---|
| Continuous Safety Monitoring | Utilizing community beef up to repair and increase considerations. |
| Cloud Agnostic | Need for lickety-split upgrades to address fresh cloud carrier aspects or adjustments. |
| Computerized Safety Assessments | |
| Alerting and Remediation |
6. Suricata

This program performs the duties of an IDS/IPS (intrusion detection/prevention/community monitoring) machine.
It has capabilities to support an eye on community online page online visitors no matter being presented in 2009.
Suricata has a location of guidelines it follows in repeat to operate well and meet your wishes.
It must always handle excessive volumes of recordsdata with out slowing down, and it gives speeds of up to 10 gigabits.
It’s additionally precious for extracting files.
To establish sophisticated threats, this open-provide instrument adjusts the settings of AWS’s steel and digital machines to mimic community exercise.
Substances
- Suricata analyzes community recordsdata in exact time, inspecting packets and protocols.
- A highly efficient principles-based detection engine in Suricata can establish chance signatures and patterns.
- Suricata reads networked files.
- Integration with chance intelligence streams improves detection
- Flexible rule management and customization
| What’s Staunch ? | What will likely be Better? |
|---|---|
| Community Traffic Diagnosis | Fallacious Distinct Management |
| Multi-Threaded and High Performance | Particular person Interface and Visualization |
| Rule-Based Detection | |
| Protocol Pork up |
7. Zeek/Bro
It’s a community monitoring instrument that, like Suricata, looks to be for out-of-the-regular exercise on networks.
The suspicious chance exercise is additionally suspected.
Unlike venerable IDS, which is a principles-based engine that can detect the chance with relative ease, this intention is extra nuanced.
As a precious community monitoring instrument, it records events as they happen and retail outlets them for later overview.
It additionally interacts and understands no matter occurred within the community security.
The Zeek programming language will even be tailored to meet the strange requirements of any alternate.
Utilizing exact a few operators like AND, OR, NOT, and heaps others., it makes it more straightforward to assemble advanced logical conditions.
Substances
- Trying at and keeping an find on community online page online visitors
- Protocol prognosis lets you find alternative what’s occurring in a community
- Creating and logging events in exact time
- A quantity of recordsdata is extracted from community online page online visitors
- A fats scripting language for custom compare
| What’s Staunch ? | What will likely be Better? |
|---|---|
| Community Traffic Diagnosis | Restricted GUI as in contrast to other security programs. |
| Protocol Diagnosis | Tuning and optimizing rule sets requires skill. |
| Extensible and Scriptable | |
| Entire Logging |
8. Panther

This sturdy utility changed into developed to address the obstacles of venerable SIEMs of more than a few flavors.
Airbnb has automatic and open-sourced this intention.
It gives centralized detection that tailors the ecosystem and skill to your company.
The principles are clear and fraudulent positives are diminished and fatigue alerts are introduced on by the transparency of every detection.
Untheorized detection is additionally detected, and this recordsdata will even be included into your machine.
That you too can discontinuance additional ruin to a make a choice few objects by having it automatically just the wrong setup.
Panther ensures that your recordsdata is mostly below your support watch over by deploying with its have AWS Cloud and AWS CloudFormation.
Substances
- platform for cloud-based security monitoring and recordsdata
- Getting and examining logs in exact-time for cloud settings
- Safety considerations are discovered and dealt with automatically
- Constructed-in detection principles and searches that will even be used exact away
- Getting alongside with huge cloud carrier companies like AWS, GCP, and Azure
| What’s Staunch ? | What will likely be Better? |
|---|---|
| Cloud Safety and Compliance | Integration with Extra Cloud Services |
| Infrastructure as Code (IaC) Pork up | Evolved Threat Detection Capabilities |
| Vast Principles Library | |
| Vast Principles Library |
9. Kali Linux
This open-provide machine gives cyber security and trying out tools.
This Linux distribution instrument for hacking entails surveillance.
It runs on Home windows 10 and entails Linux penetration-trying out tools. This helps Raspberry Pi, Odroid, HP and Samsung Chromebooks, Beaglebone, and others.
Substances
- It’s doubtless to rep out dwell starting up, and it’s uncomplicated to open.
- Toolset that’s saved up previously and modified gradually.
- Kali Linux is designed to shield your recordsdata non-public and safe.
- we can alternate loads with Kali Linux.
- we can utilize a dwell USB drive to elope Kali Linux must you actually wish to.
| What’s Staunch ? | What’s Staunch? |
|---|---|
| Entire Toolset | Balance and Compatibility |
| Easy Accessibility | Integration with Diversified Operating Systems |
| In vogue Updates | |
| Customizability |
10. PacBot

A cloud-based compliance monitoring and reporting platform with automatic security controls.
The policy as code bot (PacBot) analyzes the helpful resource in test in gentle of the established principles.
PacBot aspects an built-in auto-fix architecture that can steal remedial measures in accordance with policy infractions.
The instrument’s visualization tools create it uncomplicated to take into anecdote and fix policy infractions, to boot to gape compliance.
Substances
- PacBot checks for PCI-DSS, AWS’s Wisely-Architected Framework, and CIS Benchmark compliance
- It lets companies location and put into effect security regulations.
- Customizable workflows for policy experiences and fixes
- Rep entry to support watch over in accordance with roles and audit trails for governance
- Architecture that will even be scaled up or all of the components down to suit huge deployments
| What’s Staunch ? | What will likely be Better? |
|---|---|
| Safety Automation | Customization and Rule Introduction |
| Compliance Monitoring | Potential third-party instrument integration considerations. |
| Centralized Safety Dashboard | |
| Extensibility and Customization |
11. OSSEC
Amongst the finest detection tools, and the correct at defending a monitoring platform, this open-provide platform changed into based in 2004.
It gives flawless detection every on-premises and within the cloud.
Here’s additionally used for monitoring and examining programs like firewalls, web servers, and logs.
Apart from as to exact-time integrity monitoring, OSSEC keeps an find on security metrics for SIM and SIEM.
The program is acceptable with a wide quantity of working programs.
The monitoring is dealt with by a centralized supervisor that relays recordsdata from the agents.
The file will even be saved when the database, logs, machine auditing, events, and heaps others. had been verified for accuracy.
Substances
- OSSEC analyzes machine, utility, and community log recordsdata.
- It analyzes log recordsdata from community devices, machine logs, and utility logs.
- These policies test attack signatures and traits.
- These are malicious applications that enable unauthorized obtain admission to. OSSEC may well also just scan the machine.
| What’s Staunch? | What will likely be Better? |
|---|---|
| Intrusion Detection | Scalability and Performance |
| Accurate-Time Alerting | Enhanced Threat Intelligence Integration |
| Log Diagnosis and Correlation | |
| Active Response and Blocking off |
Closing Thoughts
To enable the safety monitoring machine, these above open-provide instrument helps to the organization to its most extent.
They are offering limitless advantages at zero rate.
Additionally Read
High 10 Finest Inaugurate Source Firewall to Give protection to Your Endeavor Community 2024
High 10 Harmful DNS Assaults Kinds and The Prevention Measures
Source credit : cybersecuritynews.com


